error: you need to load the kernel first.
Press any key to continue..._
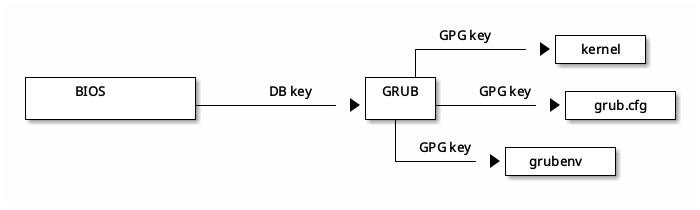
Current hypothesis is that the key used to sign grub has expired and a firmware update is required. Workaround was disabling grub (I don't have root on that laptop so can't do my own debugging). #UEFISecureBoot