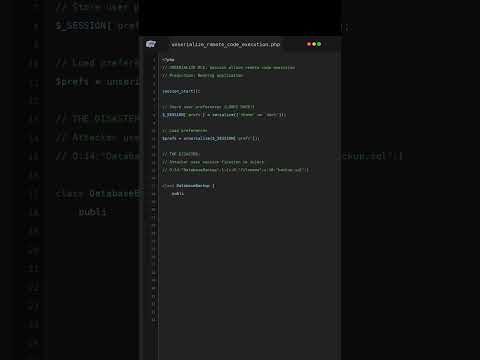
Unserialize Session Allows $47M Bank Transfer Hack?!
UNSERIALIZE APOCALYPSE! Session fixation + unserialize() = REMOTE CODE EXECUTION! Banking app backdoor installed! $47M transferred to offshore accounts! Banking license REVOKED! CTO ARRESTED!
#php #phpdisaster #unserialize #remotecodeexecution #sessionfixation #bankinghack #productionbug #phpshorts #phpwtf #$47mstolen #careerending #criminalcharges