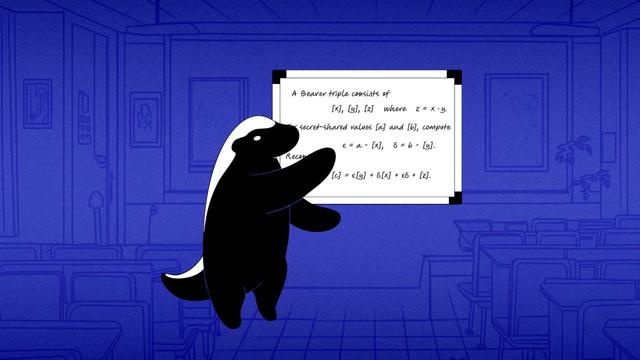
Introduction to Beaver Triples
이 글은 비버 트리플(Beaver Triples)을 활용한 비밀 분할 계산 방식을 소개한다. 친구들이 각자 식당에 대한 선호도와 지불 가능 금액을 비밀로 유지하면서도, 그룹 전체 점수를 안전하게 계산하는 문제를 다룬다. 비버 트리플은 두 비밀 공유 값의 곱셈을 다항식 차수를 증가시키지 않고 수행할 수 있게 해주며, 이를 통해 최소한의 참여자만으로 최종 결과를 공개할 수 있다. 이 방법은 랜덤 마스크를 사용해 개인 정보를 보호하면서 곱셈 연산을 가능하게 하는 핵심 기법이다. 실제 예시로 4명의 친구가 3개 식당 점수를 계산하는 과정을 상세히 설명한다.
https://stoffelmpc.com/stoffel-blog/beaver-triples-tuples
#securemultipartycomputation #secretsharing #beavertriples #privacy #multiplicationprotocol
Computing with Secret Shares - Introducing Beaver Triples - Stoffel - MPC Made Simple | Privacy-First Application Development
Ship features that can't leak user data—even in a breach. Stoffel's secure multiparty computation (MPC) platform lets you compute on encrypted inputs. Math-backed privacy, not promises.