
What Microsoft 365 Copilot flex routing means for EU businesses — an explainer | Proton
Your business data is about to automatically travel outside the EU. Here's why you should opt out and how to do it.

European tech is an investment not a cost | Proton
Businesses in Europe can reduce their reliance on US tech by investing in real digital sovereignty, not Big Tech sovereignty washing.

Proton Drive got faster and easier to use in early 2026 | Proton
From faster file transfers to smoother mobile photo browsing, here’s how strong Proton Drive started in 2026.
In rush for age checks, we’re putting kids’ security at risk - by Edward Komenda
#proton #protonblog #protonprivacy
https://proton.me/blog/is-age-verification-safe

Is age verification safe? The hidden privacy risks putting kids at risk | Proton
Is age verification safe? Learn how age checks can expose children to privacy risks, scams, and data breaches.

Age verification alternatives that protect children without sacrificing privacy | Proton
Explore alternatives to online age verification, from parental controls to zero-knowledge proofs, and how they can protect children without exposing personal data.

What small businesses get wrong about password managers | Proton
Over half of SMBs use a business password manager, but they're still not reaping the full benefits. Our research suggests solutions.
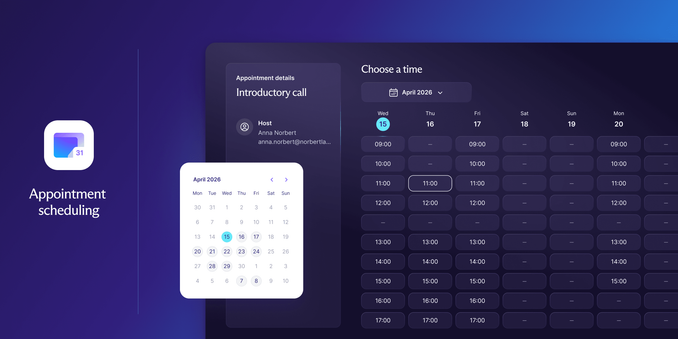
Introducing appointment scheduling tool in Proton Calendar | Proton
Share a public booking page where your colleagues, clients, or friends can schedule meetings based on your availability.
Age checks and child safety: Online age verification systems fail to protect
children - by Edward Komenda
#proton #protonblog #protonprivacy
https://proton.me/blog/online-age-verification-child-safety
Online age verification systems fail to protect children | Proton
Do online age verification systems improve child safety? See how age restrictions and age checks fall short, and what that means for privacy and protection.
What happens after age-verification laws take effect: The chilling effect of
online age and ID checks - by Edward Komenda
#proton #protonblog #protonprivacy
https://proton.me/blog/age-verification-laws-chilling-effect

What happens after age verification laws take effect | Proton
Age verification laws are reshaping the internet. See how ID checks, age filters, and platform rules create chilling effects on speech, access, and privacy.
What age verification actually means (and why the term is misleading) - by Edward Komenda
#proton #protonblog #protonprivacy
https://proton.me/blog/age-verification

Age verification explained: what it is, systems, software, and risks | Proton
What is age verification? Learn how age verification systems, software, and age checks work, including age estimation, age filters, and privacy risks.