Log4Shell
TIL about the breakdown of the Log4Shell shared library.
- Date of occurence
- 24 November 2K21
- location of programmer at home with his son logging into minecraft (which failed)
- this vulnerability had existed unnoticed since 2013
- it was privately disclosed to the Apache Software Foundation { Log4j is a project}
- discloser: Chen Zhaojun of Alibaba Cloud's infosec team
- date 24 November 2021
- exploit severety MAXIMUM
- It's simple to execute
- estimation of affect ration of 50% of the internet (many hundreds of millions of devices)
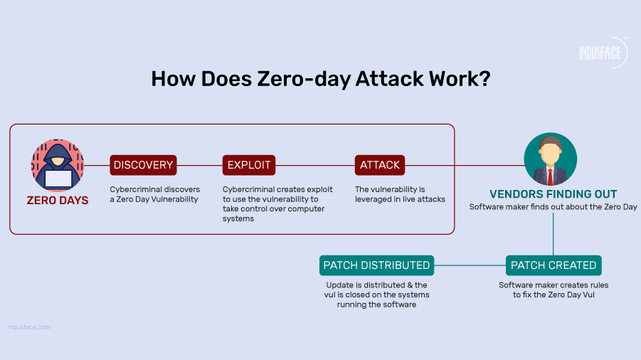
- vulnerability abuses Log4j allowing requests to arbitrary LDAP and JNDI servers
- that allows attackers to
- execute arbitrary Java code on server / client
- leak sensitive data
Innerworkings
- Log4j
- open-source logging framework
- enables programmers to log data within their applications
- can include user input
- is used ubiquitously in Java programs especially enterprise software
- Originally written in 2001 by Ceki Gülcü
- part of Apache Logging Services
- project of the Apache Software Foundation
Tom Kellermann, a member of President Obama's Commission on Cyber Security
- Apache is "one of the giant supports of a bridge which facilitates the connective tissue between the worlds of applications and computer environments
Affected commercial services
- Amazon Web Services {AWS}
- Cloudflare
- iCloud {Apple infrastructure}
- Minecraft: {Java}
- Steam {multi platform gaming}
- Tencent QQ### Wiz and EY sate that the vulnerability affected 93% of enterprise cloud environments
The Log4Shell vulnerability's disclosure received strong reactions from cybersecurity experts.
Cybersecurity company Tenable stated
- exploit is "the single biggest, most critical vulnerability ever## Ars Technica
- arguably the most severe vulnerability ever
Quote
Log4j is foundational software. This 20+ year-old Java logging library quietly powers system events in applications worldwide, like user logins and calculation results. But this small piece of software had quietly become a dependency in thousands of projects across the Java ecosystem.
Opinion & reaction
- I'm blown away by the events leading to the tornadoes & typhoons that followed shortly after in the OpenSource programming World
- Fifty percent of software was affected with 93% of enterprise software sub section
- Log4Shell is a critical infrastructure level shared library
- nearly everyone using java depends on it's functional I/O
Analysis
- why do most Open Source software users only contact programmers when bugs are detected?
- why do they (almost) never get compliments when it goes well?
- programmers burn out after a while and leave projects abandoned
- when you were a kid, your mom / dad / family complimented you on good results
- programmers need the same
- otherwise they will leave the projects
Open Source programming is a thankless job
- Zero cash influx
- no thank you's
- complaints even when software has long matured to stable levels
- entitled users
- threats to be Doxxed or worse
Be nice to Open Source programmers
- If you have following contact here on the Fediverse with one say thank you
- don't expect replies (esp when hundreds to thousands of followers are indicated)
- realize you either can't code programs of that caliber or don't want to invest the time
- I am lucky to have conversational contact ont the FediVerse with critical infrastructure programmers
- I always say thank you, because I know how hard it is to write software of that magnitude
- when I review their software, I am critical, but formulate my words and sentences in a manner I would want to read them if places were switched
- I am thankful first, thus send them Universal Love and Universal Energy
- My toot history stand for these statements (on my other Fediverse accounts)
Don't be a dick!
Be nice to programmers
Give them Love
Z
#Log4Shell #TIL #programming #data #Java #exploit #ZeroDay #technology #Enterprise #networking #OpenSource #POSIX #BSD #freeBSD #ghostBSD #openBSD #Linux #win64 #mac #history #reading
Sources:
https://github.blog/open-source/inside-the-breach-that-broke-the-internet-the-untold-story-of-log4shell/
https://en.wikipedia.org/wiki/Log4Shell