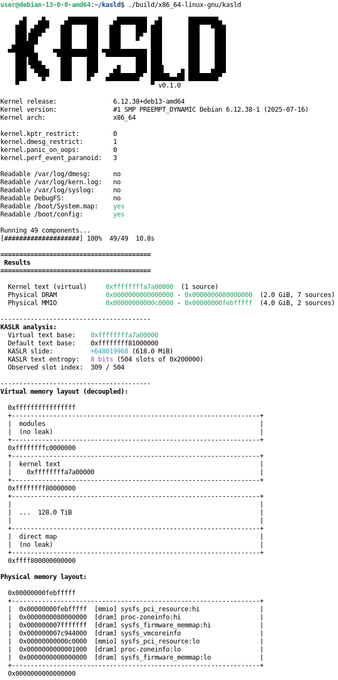
KASLD v0.1.0 released.
New orchestrator runs and cross-correlates leak components to map kernel memory layout. Computes #KASLR slide, entropy bits, and renders virtual/physical memory maps.
19 new components including prefetch side-channel. Cross-compiles for 13 architectures.