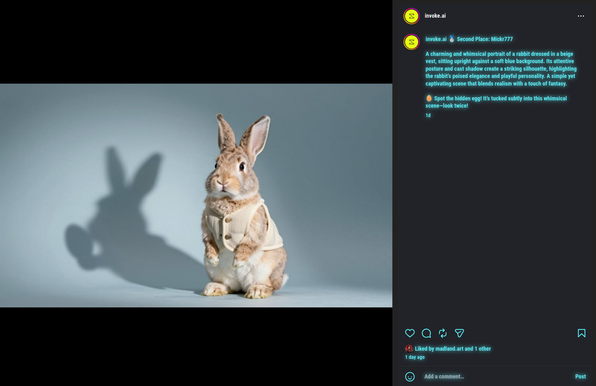
Honestly, I'm shocked this joke made runner-up. 😉🥚
InvokeAI 6.10 with Z-Image Turbo Support
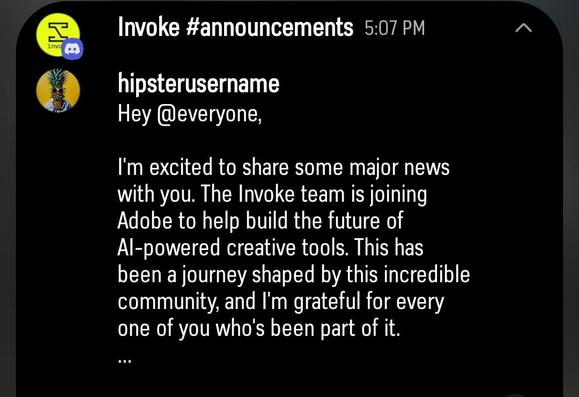
The developers of InvokeAI were acqui-hired by Adobe a few months back, and this could have been the end of the project. But as an open source project, some of the other developers have picked up the ...
https://potentialx.ca/link/2026/01/06/invokeai-6-10-with-z-image-turbo-support/
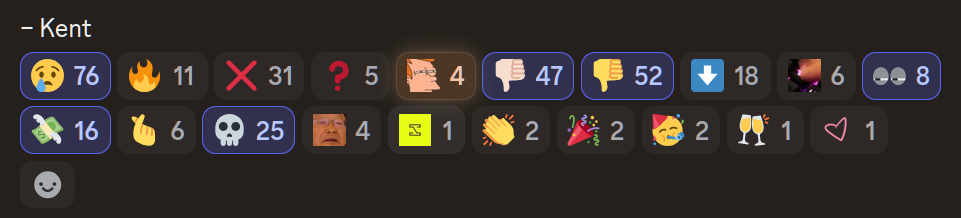
Two lessons learned from the #InvokeAI acquisition announcement:
- You need to pause and think through both what you say, and how the public will react to it. Try to step outside your inner circle bubble and think about the greater community. Anticipate their questions and reactions and include that in the announcement -- don't just rush to the Discord #Announcements channel to show off how fat your bank account is going to be. A subsequent FAQ post in the hours after won't get nearly as much traction as the initial announcement. It's like a pebble being thrown into the wake of a motor boat.
- If you sell out, understand that WHO you sell out to will affect your reputation. Grudgingly, I accept that the desire for many is to make a thing and cash out, that being the 'win condition'. But #Adobe is rightly reviled in the modern era. The idea of them being anywhere near Invoke is a nightmare scenario. While the community edition may continue to be "open source and free", there's very little chance I'm going to want to contribute (in the wake of the core developer vacuum left by this) if it means my work is going downstream to help Adobe in any way. (Not everyone will feel that way, of course -- many happy PRs to you.)
GitHub - LuqP2/local-image-browser-for-invokeai https://github.com/LuqP2/local-image-browser-for-invokeai
https://github.com/Acly/krita-ai-diffusion?tab=readme-ov-file
GitHub - Acly/krita-ai-diffusion: Streamlined interface for generating images with AI in Krita. Inpaint and outpaint with optional text prompt, no tweaking required.
Streamlined interface for generating images with AI in Krita. Inpaint and outpaint with optional text prompt, no tweaking required. - Acly/krita-ai-diffusion
📝 **CVE-2024-12029** est une vulnérabilité de désérialisation critique dans l'API d'installation de modèles d'**InvokeAI** qui permet une **exéc...
📖 cyberveille : https://cyberveille.ch/posts/2025-07-18-vulnerabilite-critique-de-deserialisation-dans-l-api-d-installation-de-modeles-d-invokeai/
🌐 source : https://www.offsec.com/blog/cve-2024-12029/
#CVE_2024_12029 #InvokeAI #Cyberveille
Vulnérabilité critique de désérialisation dans l'API d'installation de modèles d'InvokeAI
CVE-2024-12029 est une vulnérabilité de désérialisation critique dans l’API d’installation de modèles d’InvokeAI qui permet une exécution de code à distance sans authentification. La faille provient de l’utilisation non sécurisée de la fonction torch.load() de PyTorch lors du traitement des fichiers de modèles fournis par l’utilisateur. Les attaquants peuvent concevoir des fichiers de modèles malveillants contenant du code Python intégré qui s’exécute lorsque le modèle est chargé côté serveur. La vulnérabilité affecte les versions 5.3.1 à 5.4.2 d’InvokeAI et a reçu un score CVSS de 9.8. Les organisations doivent immédiatement mettre à jour vers la version 5.4.3 ou ultérieure et mettre en œuvre une validation d’entrée appropriée ainsi que des contrôles de segmentation réseau.