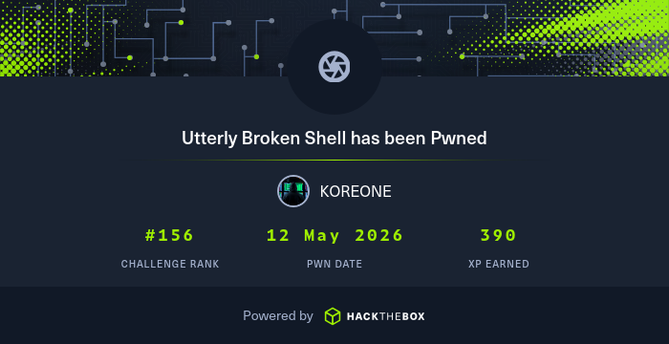
Damn man... what a box! Really nice experience 💪
Working through the HTB Windows PrivEsc module I keep drowning in edge cases.
I tried to distill what actually matters when you're starting out/ preparing for a cert, e.g.:
SeImpersonate → SYSTEM in one tool call. DnsAdmins → malicious DNS DLL. Server Operators → service binary hijack. And always whoami /all, not just whoami /priv.
Full walkthrough + real shell output:
niklas-heringer.com/skills-lab/windows-privilege-escalation-02-privesc-paths/
rootsecdev (@rootsecdev)
fail-copy 개념증명(POC)이 공개되자 이를 바탕으로 클린 익스플로잇을 만들었고, 재부팅 없이도 대상 서버의 UID를 수정하는 후속 공격까지 구현했다는 내용이다. CTF와 Hack The Box 환경에서 활용 가능성을 강조한다.
just dropped Windows PrivEsc 01: Initial Enumeration
the part where HTB boxes stop being "just like Linux" hihi
network recon, Defender/AppLocker analysis, process hunting, patch enumeration. command output, reasoning behind every step and quizzes to memorize them
part 1 of a series:
https://niklas-heringer.com/penetration-testing/windows-privilege-escalation-01/
#pentesting #windows #infosec #hackthebox #ctf
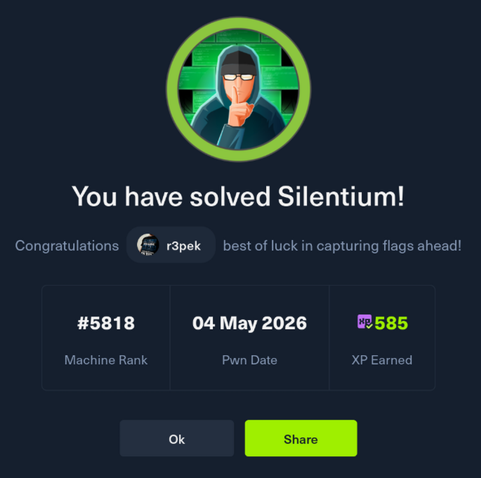
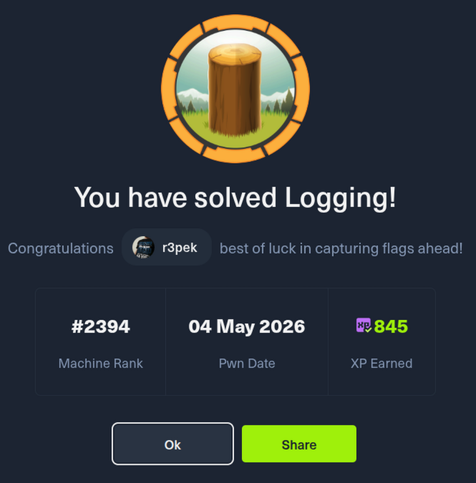
Finally finished the "Penetration Tester" path on Hack The Box Academy, which now makes me eligible to at least try the CPTS certificate.
To be honest, going through all this without much beforehand knowledge or experience was a lot. But it was mostly interesting and fun. Took way longer than expected to finish this (mostly in my spare time).
Next stop, train and try to get this CPTS certificate in the not too distant future.
https://academy.hackthebox.com/achievement/badge/2d5c46db-3c06-11f1-9254-bea50ffe6cb4
https://www.hackplayers.com/2026/04/boxpwnr-resuelve-maquinas-de-hackthebox-con-IA.html