EURACTIV Italia on Instagram: "Euractiv Italia ha intervistato Sandro #Gozi, parlamentare europeo di Renew Europe, segretario dello European Democratic Party, presidente dell’Unione Europea dei Federalisti, coordinatore del Gruppo Spinelli, che riunisce i parlamentari europei più federalisti. "Dobbiamo lavorare per mettere l’Unione Europea nelle condizioni di costruire una vera Unione della #difesa e dell’#energia. Questo si fa in buona parte anche attraverso una #revisione dei Trattati", ha detto Gozi. Leggi l'intervista completa nel link in bio ☝️ ✍️ @castaldi_roberto 📸 Luca Gualco - EURACTIV Italia"
3 Likes, 0 Comments - EURACTIV Italia (@euractiv.it) on Instagram: "Euractiv Italia ha intervistato Sandro #Gozi, parlamentare europeo di Renew Europe, segretario de..."
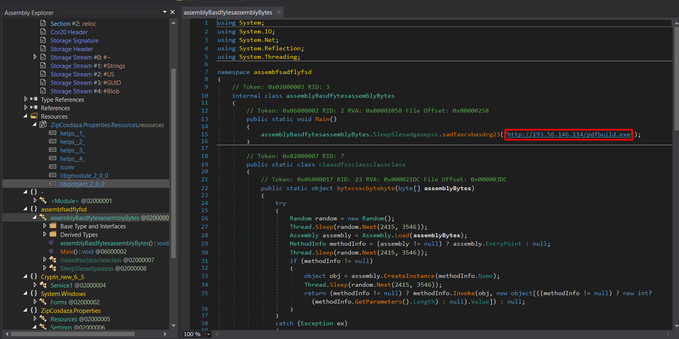
Found in the wild! Allegedly Gozi malware stage 1.
Attack path:
phishing -> xlsx macro -> chechoa[.]com -> commandline calc.exe -s 6636702. -> Stage 2
https://bazaar.abuse.ch/sample/eef902138fc1ee637b41bbecd442a64b691b5b9aae15d2c822ac983ef93e4616/
Current #payloads:
-ZipCosdaz.exe (#RedLine)
C2: 193.56.146.114:44271
Botnet: NewBuild
- ZipCosdaz1.exe (#Ursnif aka #Gozi)
C2 servers:
45.11.182.97
79.132.128.108
91.241.93.98
79.132.128.109
91.242.217.28
91.241.93.111
Botnet: 2503
- ConsoleDWS.exe (Destroy Windows 10 Spying)
GitHub repo: https://github.com/spinda/Destroy-Windows-10-Spying
+ And another download URL: archiverportal[.]space/porn.php
Malspam campaign sent from compromised email accounts, distributing #Gozi in Italy Spammed Excel (XLS) is completely undetected by AV
XLS:
https://bazaar.abuse.ch/sample/4b462d7cd8e4ba2d1da7332df73f99f89a4da71357fb855e9b9e8cc3949f40d6 …
EXE:
https://bazaar.abuse.ch/sample/d04ce36b2c6a5888bf4c413ed5a1c8d2e16af857957742059e7f4de74d36d854 …
Payload URL:
https://urlhaus.abuse.ch/url/350489/ pic.twitter.com/skuPg75WYS