#Gootloader is a highly active banking Trojan-turned-loader #malware that has recently appeared on multiple vendors’ priority threat lists, attacking organizations in a wide range of verticals & countries. If your leadership or other stakeholders asked for a list of this threat's most common TTPs, would you be able to provide it quickly?
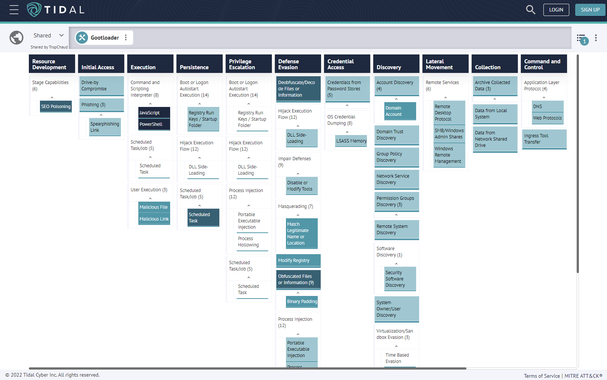
Now you can, with the Gootloader #TTP matrix available in Tidal’s free Community Edition: https://app.tidalcyber.com/share/796cacb6-3bb1-474b-9747-abcce2c47de2
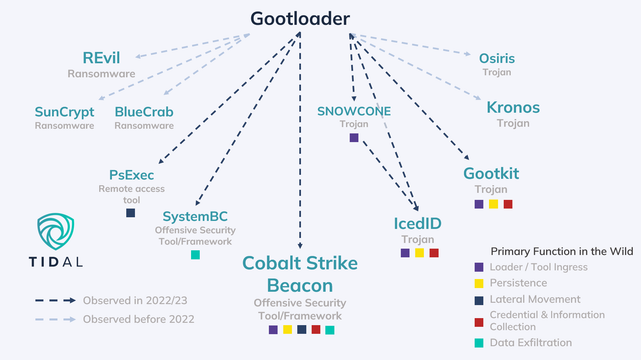
Gootloader, also referred to by its related payload, #Gootkit, first emerged in 2014 but has been especially active since 2020. Despite this, technical reporting around its TTPs has been relatively light until even more recently. In the past two years alone, verticals including finance, #healthcare, defense, pharmaceutical, energy, & automotive have faced Gootloader campaigns, with victims across North America, Western Europe, & South Korea, and the malware is regularly used to deliver high-impact payloads, including Cobalt Strike, #IcedID (a common #ransomware precursor), & more. Industry-based #threat profiling can be a powerful tool, but even if your industry (or your corner of it) hasn’t yet directly observed Gootloader activity, we believe broad-based threats like this should be on most teams’ radars
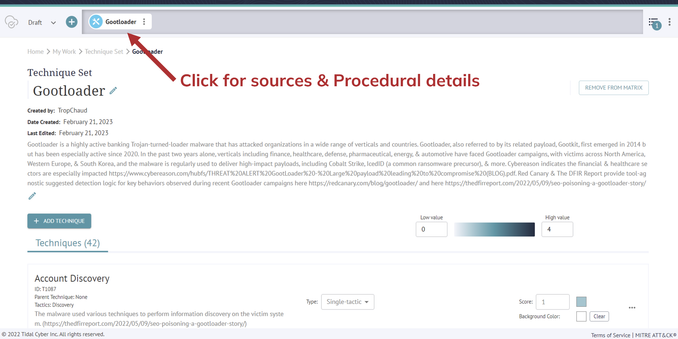
Our matrix summarizes Gootloader TTPs detailed across several great recent technical reports. Reports from SentinelLabs, Cybereason, & The DFIR Report were helpfully pre-mapped to #mitreattack, and we mapped a couple other detailed analyses. Procedural details are even available for nearly all the included technique mappings – be sure to click the Technique Set’s label in the ribbon at the top of the screen to pivot into the Details page with this information & relevant source links throughout
Red Canary & The DFIR Report helpfully provided tool-agnostic suggested #detection logic for key behaviors observed during recent Gootloader campaigns here https://redcanary.com/blog/gootloader/ and here https://thedfirreport.com/2022/05/09/seo-poisoning-a-gootloader-story/. Take a wider view by layering entire segments of your defensive stack over the #CTI back in the Community Edition, by toggling on any of the mappings available in @tidalcyber's Product Registry https://app.tidalcyber.com/vendors
#SharedWithTidal #threatinformeddefense #CobaltStrike #initialaccess #blueteam