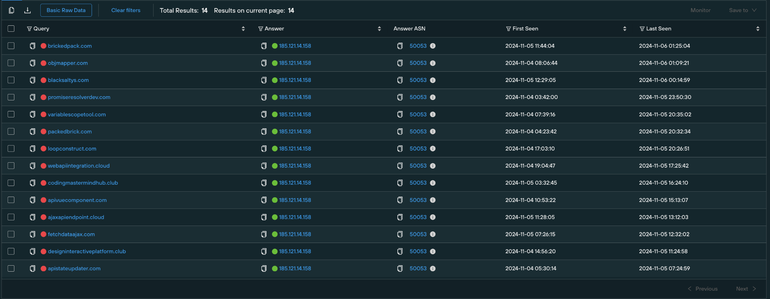
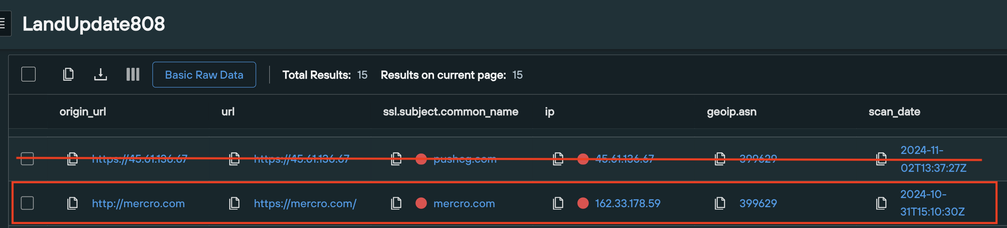
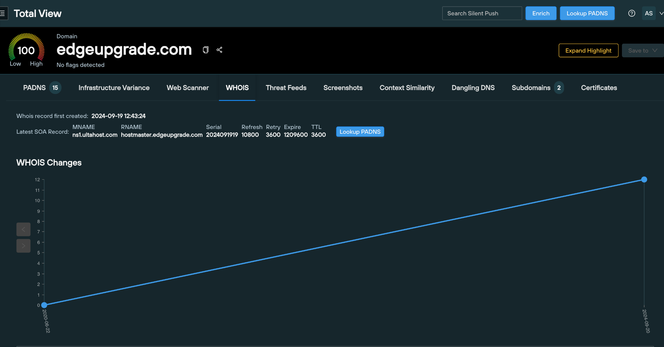
Testing out Chris Duggan's DNS Coffee workflow (https://x.com/TLP_R3D/status/1845446668549775372) to search for new TA582 domains.
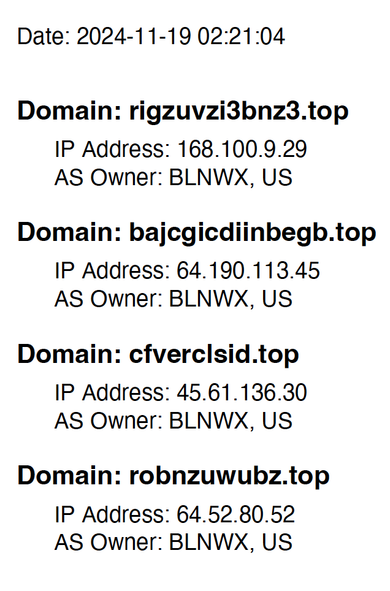
New #TA582 domains observed via the workflow:
pbizntettbvs[.]top
rigzuvzi3bnz3[.]top
robnzuwubz[.]top
Chris Duggan (@TLP_R3D) on X
🧵Thread / 🕵️♂️ Ever wanted to hunt down APTs like #TheCom via DNS but can't be bothered with all the searching and clicking? Want to get a list of interesting 'live' domains to investigate in under 60 seconds ⏰!! No worries! Let's automate the process with a Python script