#Sydbox 3.55.0 is released! Introduces Domain Transitions to change sandbox policy manually or based on a set of events. IPC thread is hardened to set a limit on max connections and disconnect idle connections. Includes some minor security fixes for sandbox capabilities as well. Full story: https://gitlab.exherbo.org/sydbox/sydbox/-/blob/main/ChangeLog.md #exherbo #linux #security
News from #Sydbox #git: As of version 3.55.0, bind mounts are secure by default. Regardless of whether the source is an absolute path or a filesystem type, every bind is mounted with nodev, noexec, nosuid, and nosymfollow options applied. User must therefore explicitly opt back into the relaxed behaviour upfront using the options dev, exec, suid and symfollow: https://man.exherbo.org/syd.2.html#bind #exherbo #linux #security
News from #sydbox #git: We have #Caitsith like Domain Transitions now which allows you to change sandbox policy atomically either manually or upon certain events such as exec, chdir, mmap, bind, connect, accept. One example would be restricten the confinement of a web server upon first bind another example is per-directory sandbox policies. There're many other nice uses, see examples: https://man.exherbo.org/syd.7.html#Domain_Transitions #exherbo #linux #security
#Sydbox 3.54.1 released! Security release with fcntl(2) hardening against SIGIO bypass of #landlock signal scoping. Adds log rate limiting with log/rlimit_interval and log/rlimit_burst options. New deleted file access mediation denies unlinked files through open fds. chown(2) confined to caller's credentials by default, force_umask default now 7000 for setuid/setgid/sticky stripping like #OpenBSD #pledge. Ghost mode implies lock:on. Full story: https://gitlab.exherbo.org/sydbox/sydbox/-/blob/main/ChangeLog.md #exherbo #linux #security
#Sydbox containers are not affected by the new LPE #Fragnesia because: 1. Unprivileged user/network namespaces are denied unless trace/allow_unsafe_namespace:user,net 2. Kernel algorithm (AF_ALG) sockets are denied unless trace/allow_unsafe_kcapi:true 3. Socket option TCP_ULP is denied unless trace/allow_unsafe_setsockopt:true. You may sleep in peace: https://raw.githubusercontent.com/v12-security/pocs/d4043edc2acbd75d093e3f5795751b678c66b259/fragnesia/fragnesia.c #exherbo #linux #security
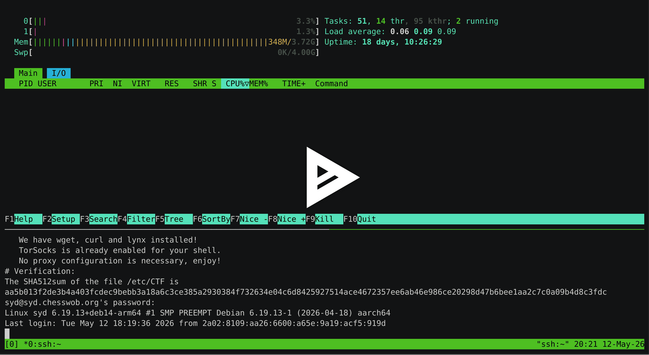
I made an #asciicast showcasing Ghost Mode of #sydbox: https://asciinema.org/a/1039185 #exherbo #linux #security
#Sydbox 3.53.0 is released! This is a feature release improving sandbox categories walk, stat, and adding the new category list for directory listing which allows easy use of walk+list categories for path hiding. readlink is also split from stat category which is by far the most common syscall so this helps with overhead of other categories. We also have bunch of security fixes. Full story, as always, is in the ChangeLog, thanks for flying Syd: https://gitlab.exherbo.org/sydbox/sydbox/-/blob/main/ChangeLog.md?ref_type=heads#3530 #exherbo #linux #security