Missing from @drscriptt 's list are AAAA, HTTPS, and SVCB records.
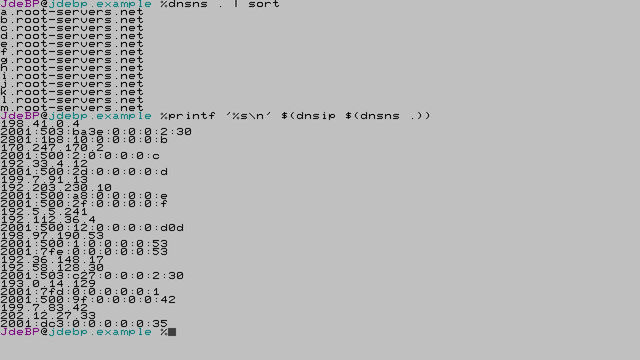
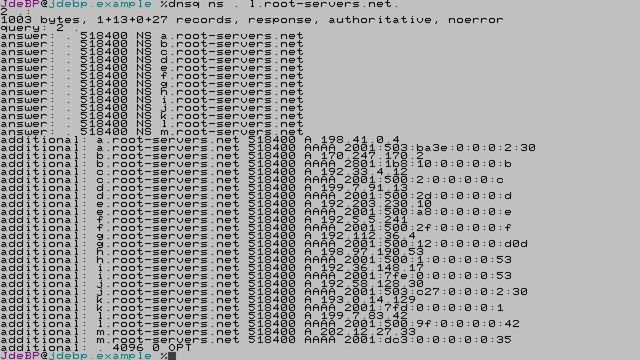
AAAA has plenty of obvious choices.
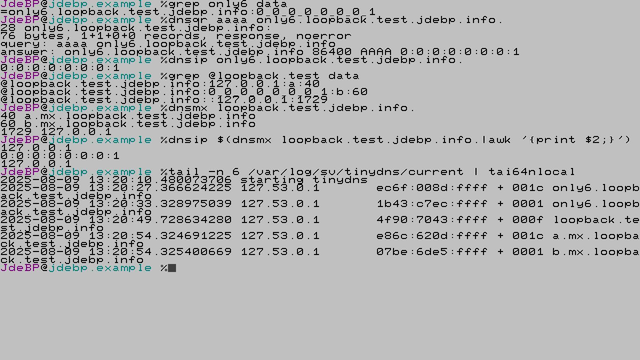
You'll know the . convention for SRV, SVCB, and MX resource record sets, of course.
I shall just drop in my personal experience from earlier this year that an accidentally supplied HTTPS resource record can *definitely* break WWW traffic; because browsers in practice do not obey RFC9460 §2.4.2.
#djbdns
#DomainNameSystem
#SplitHorizon
#ReservedSuperDomains #DNS #HTTPS #SVCB