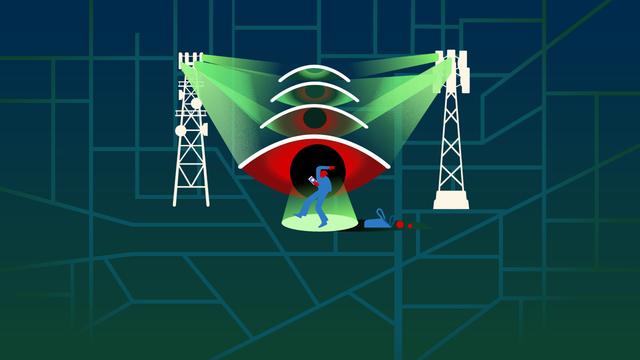
📢 Citizen Lab expose deux campagnes de surveillance télécom via SS7/Diameter et SIMjacker
📝 ## 🔍 Contexte
Publié le 23 avril 2026 par le Citizen Lab (Université de Toronto), ce rapport de rec...
📖 cyberveille : https://cyberveille.ch/posts/2026-04-24-citizen-lab-expose-deux-campagnes-de-surveillance-telecom-via-ss7-diameter-et-simjacker/
🌐 source : https://citizenlab.ca/research/uncovering-global-telecom-exploitation-by-covert-surveillance-actors/
#CSV #Diameter #Cyberveille
Citizen Lab expose deux campagnes de surveillance télécom via SS7/Diameter et SIMjacker
🔍 Contexte Publié le 23 avril 2026 par le Citizen Lab (Université de Toronto), ce rapport de recherche documente deux campagnes distinctes de surveillance télécom menées par des acteurs désignés STA1 et STA2, identifiés comme des vendeurs commerciaux de surveillance (CSV) opérant probablement pour le compte d’États. L’investigation a débuté fin 2024 suite à l’analyse de logs de pare-feu de signalisation mobile, en collaboration avec Cellusys, Telenor Linx, Roaming Audit et P1 Security.