Hello again! 
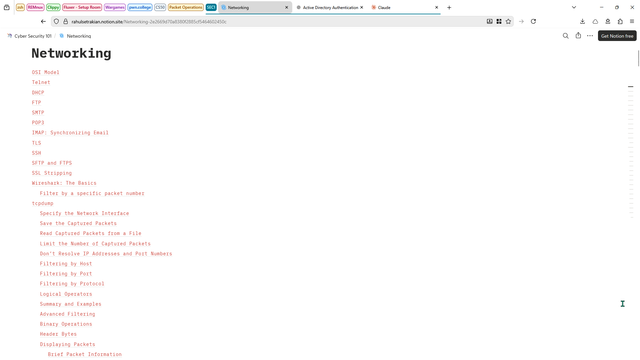
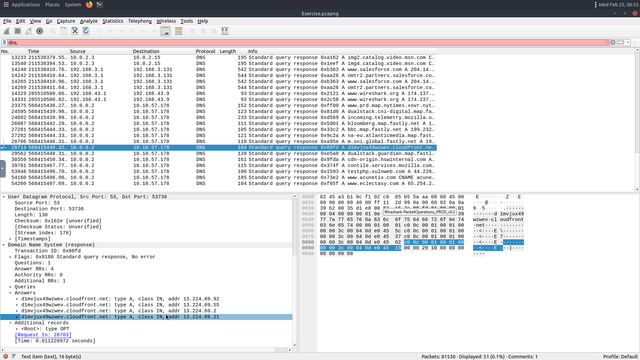
Today I reviewed tools like TCPdump and Nmap, both part of the Cybersecurity 101 networking module. I'm already comfortable analyzing packets with Wireshark, but combining it with the command-line tool TCPdump allows me not only to capture live traffic but also to read and analyze .pcap files directly from the terminal.
Starting tomorrow, I'll move into cryptography theory and begin working with tools like John the Ripper and Hashcat for password cracking practice.
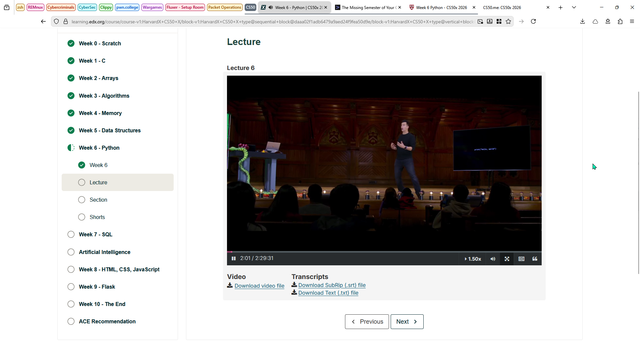
For CS50, I completed the main lecture today. Tomorrow I'll finish the remaining lecture segments and then jump straight into the problem sets.
Hello again! 
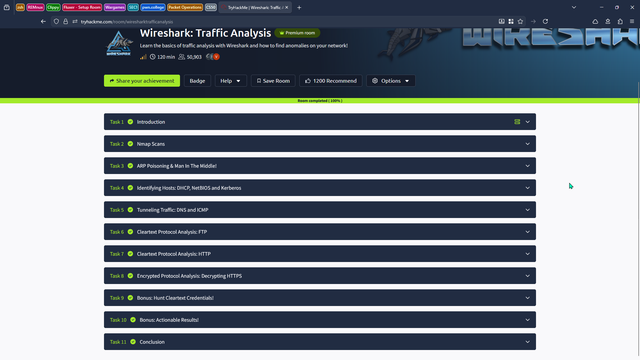
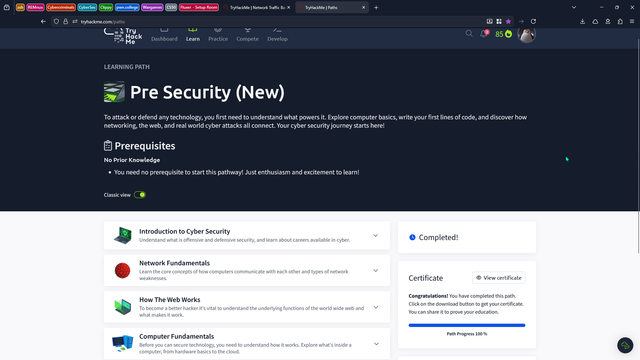
I am happy to announce that I have finally achieved a 100-day streak on TryHackMe! In addition, I reviewed some old concepts with the TryHackMe recap.
I have also reviewed basic networking protocols and practiced with them, such as Telnet, SMTP, and DHCP.
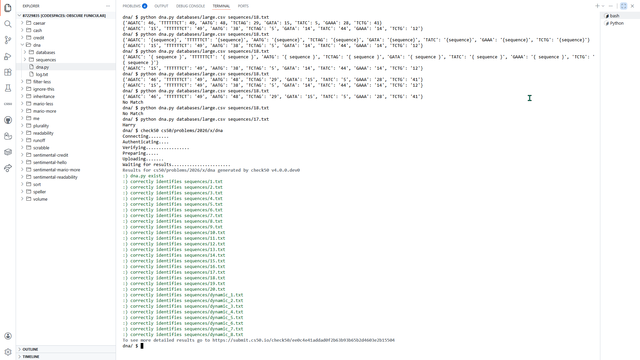
Lastly, I successfully solved the DNA problem set and figured out how to work with dictionaries, iterate through them, and use dictionary comprehension with the CSV module. Tomorrow, I will study and work on the SQL problem set.
Hello again! 
Today, I reviewed Linux Terminal commands, Command Prompt commands, and finally, PowerShell. Understanding Powershell was extremely useful because I have had less exposure to it than to Terminal and CMD.
After reviewing the CLI material, I moved on to networking concepts with practical use cases. This will greatly boost my learning.
Lastly, I worked on a DNA problem set in the Python section of the CS50 course. I'm working with CSV files and trying to create a program that performs DNA profiling.
Hello again! 
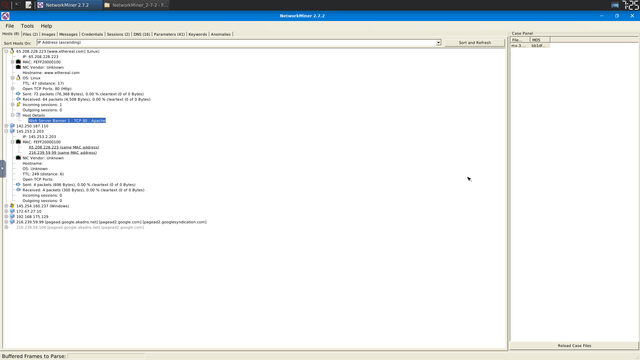
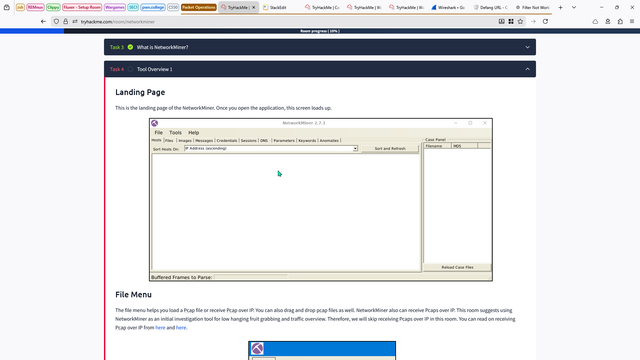
Started Monday by finishing the remaining Wireshark rooms, covering the last features and protocols. Tomorrow I'll move on to solving some traffic analysis challenges.
I also completed the Readability problem set from CS50 in Python. Next up is the DNA problem set, and after that I'll begin the SQL section.
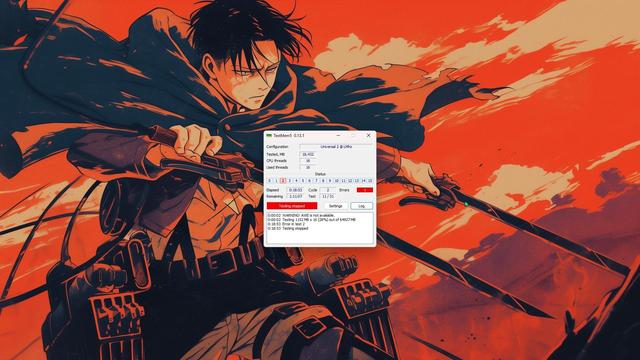
Lastly, I tracked down the cause of the system instability. After running TestMem5, the issue appears to be RAM-related. I'm now testing each stick individually to determine whether the problem is a faulty module, an unstable stick, or a motherboard slot issue. Once I isolate the cause, I'll address it.
Hello, again 
Another horrible day, the electricity was officially cut for more than 18 hours, no water, no electricity.
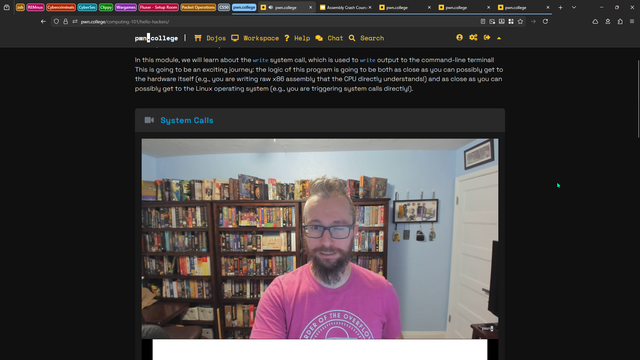
I did try to salvage this day, by doing a little bit of assembly, specifically working on different kind of system calls like write and read, while understanding how all of this connects well with C. Everything is connected.
Since yesterday, I couldn't do CS50 due to no electricity, I am gonna finish up the lectures on python, though I am already pretty comfortable with writing python code.
Hello, again 
Today is officially the worst day of this month, no electricity whole day, I wasn't able to get much done, I did do a little bit of packet analysis.
I can confidently identify common nmap scans. It all boils down to the TCP three way handshake for the TCP connect scan, and Stealth scan.
UDP scan utilizes the icmp protocol to scan the open ports.
Hello, again 
Today is a special day because two great things happened to me. First, I reached the top one percent of @RealTryHackMe. That was one of my goals for this year, so congratulations to me! Now, I have set my sights higher. I want to reach the top one thousand rank on TryHackMe.
Something extraordinary happened today. I was in the GingerHacker Initiative Discord community chatting with the founder. Since I spent my savings on the TryHackMe premium annual subscription, I told him how I'm preparing for SEC1 because it's practical and more affordable than Security+. He immediately offered to sponsor my certification to help me progress in my career. He decided to sponsor both SEC0 and SEC1. Shout out to the #GingerHacker!
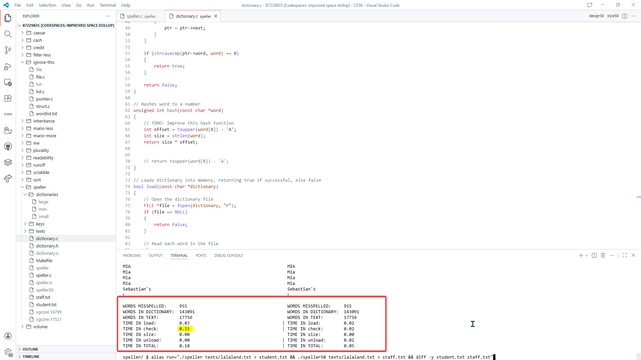
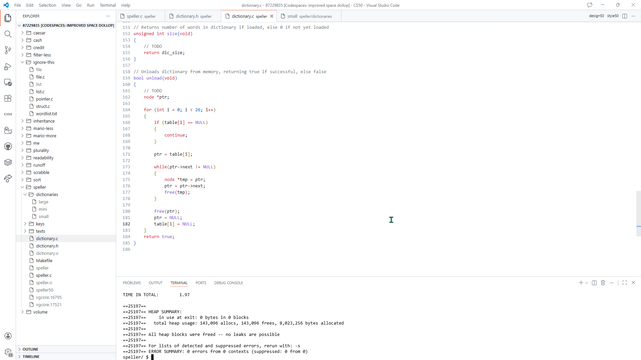
It was a crazy and wonderful day! Also, I submitted the speller problem, and now I'm moving to week six.
Python rocks! 💪
Hello, again 
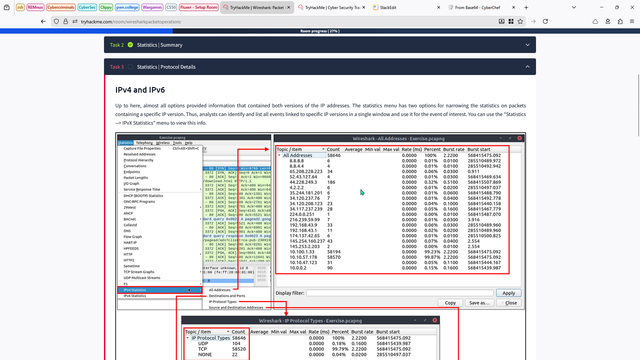
Today, I started working through the network analysis rooms on TryHackMe. I used Wireshark to analyze PCAP files, which went smoothly since I have experience with it. However, I learned how to use statistics more effectively.
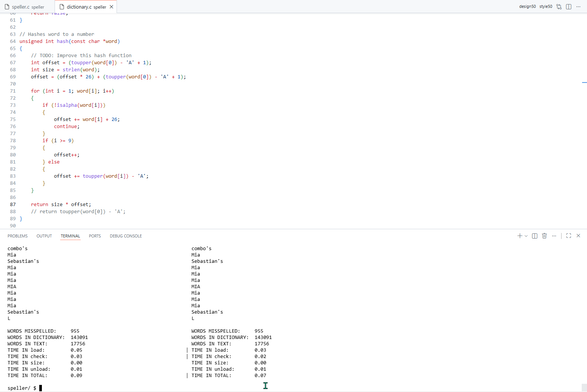
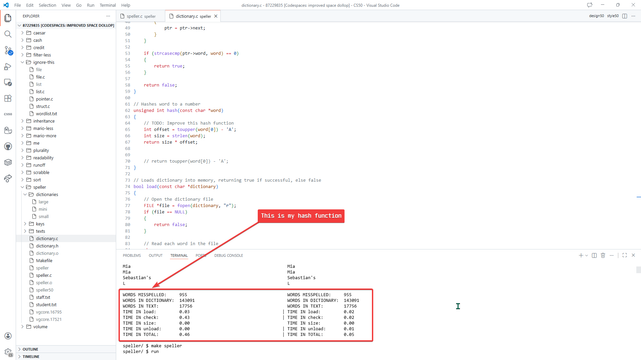
Lastly, I found a way to reduce collisions using a better hashing function. Instead of using just the first character to build the hash table, I multiplied the characters to increase entropy. I'm only six seconds behind the staff algorithm.
I also found a way to handle the apostrophe. Since I subtract 65 from the characters, the result is negative, which leads to a segmentation fault. I simply used a conditional statement to handle it.
Hello, again 
Today, I finished the remaining rooms in the Pre-Security Pathway. I reviewed programming concepts and the CIA triad, and I can finally focus on the network analysis rooms.
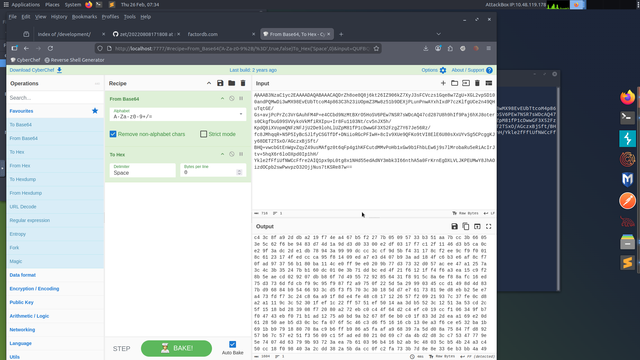
I also solved several interactive challenges involving the Caesar cipher to demonstrate symmetric encryption, and they were genuinely fun to work through.
Next, I was almost able to complete the speller code, but it still suffers from low performance because I have not yet improved the hash function, which I will work on tomorrow.
I am using a hash table with linked lists for collision handling. Currently, it takes O(n) time in practice due to poor distribution. Collisions are handled using chaining, where each bucket stores a linked list. However, I am only using 26 buckets, and the hash function returns a value based solely on the first character of the word. Each new node is prepended to the list.
As a result, lookups require linear traversal through long linked lists, which significantly impacts performance. Tomorrow, I will work on improving the hash function and compare the results.