#Canvas login portals for 15,000 institutions, including top universities like Harvard and Oxford, has exfiltrated 3.65 terabytes of student and faculty data in their boldest attempt at monetizing stolen data since announcing itself as #ShinyHunters in 2020.
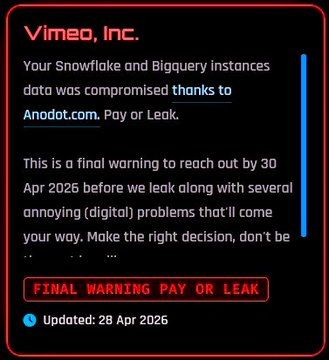
This massive black hat #BigEdu data security attack runs alongside concurrent supply chain grift attacks on corporate players like #Vimeo #WynnResorts #Snowflake and #Zara, exposing critical flaws in #EdTech & #Corporate #InfoSec partcularly protocol for third-party vendor trust.
The nefarious #ShinyHunters cabal has infiltrated over 400+ organizations in #SAAS & #DRM data breaches including #Google #Salesforce #Workday, #Crunchbase, #Gucci, #Coinbase, and #Qantas airlines not to mention so called "Security" professionals such as #CrowdStrike and #ADT
https://www.pcmag.com/news/video-platform-vimeo-hacked-by-shinyhunters-gang
https://www.docontrol.io/blog/shinyhunters
https://www.securityweek.com/wynn-resorts-says-21000-employees-affected-by-shinyhunters-hack/
https://www.reco.ai/blog/shinyhunters-data-breach-vs-saas-why-dynamic-security-matters