Alerta en Windows: Un parche incompleto permite ataques «Zero-Click»
Una falla en la actualización de seguridad de Microsoft ha dejado una puerta abierta para que hackers vinculados a Rusia ejecuten ataques sin necesidad de interacción del usuario, poniendo en riesgo datos sensibles en toda Europa (Fuente Akamai).
La seguridad de Windows se enfrenta a una crisis de confianza tras el descubrimiento de un parche defectuoso. Según un informe de Akamai, una corrección lanzada inicialmente en febrero para mitigar una vulnerabilidad en SmartScreen resultó ser insuficiente. Este parche incompleto ha dado lugar a una nueva vulnerabilidad crítica (identificada como CVE-2026-32202), que permite ataques del tipo «Zero-Click» (sin clics). En estos ataques, el simple hecho de que un usuario visualice una carpeta que contenga un archivo malicioso permite al atacante forzar una autenticación automática con su servidor, robando las credenciales del usuario sin que este se dé cuenta.
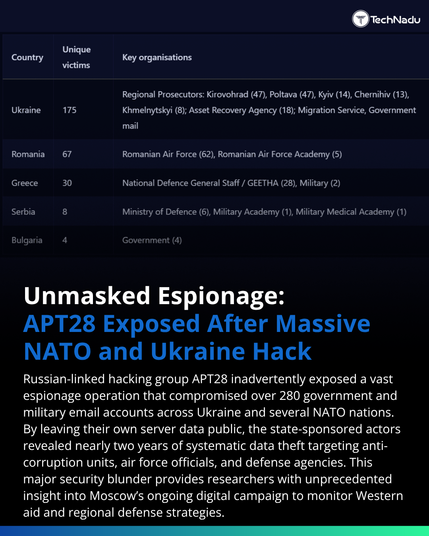
El grupo de ciberespionaje ruso APT28 (también conocido como Fancy Bear) ha sido identificado como el principal explotador de esta brecha. Los investigadores señalan que el grupo ha estado utilizando archivos de acceso directo (.lnk) modificados para saltarse las protecciones de Windows y ejecutar código remoto. Al aprovechar el mecanismo de procesamiento de iconos de Windows Explorer, los atacantes logran que el sistema de la víctima envíe su «hash» de autenticación NTLM a un servidor remoto, lo que facilita el robo de identidad y el movimiento lateral dentro de redes corporativas y gubernamentales, especialmente en Ucrania y países de la Unión Europea.
Microsoft ha incluido una nueva corrección para este fallo específico en su tanda de parches de abril de 2026. Sin embargo, la persistencia de estas brechas subraya la complejidad de parchear sistemas heredados como Windows Shell y el framework MSHTML. Los expertos en ciberseguridad recomiendan encarecidamente a las organizaciones aplicar las últimas actualizaciones de forma inmediata y considerar la desactivación de protocolos de autenticación antiguos como NTLM en entornos sensibles para prevenir este tipo de «coerción de autenticación» que la IA y los grupos estatales están empezando a explotar con mayor frecuencia.
#akamai #apt28 #ciberseguridad #PORTADA #zeroClick