Facebook’s account system is absurdly permanent. Delete an account and you’re locked out for good — can’t reuse your email, can’t start fresh, no appeal, no second chance. Even username‑based platforms handle identity better. Facebook’s “account integrity” model traps real users instead of helping them.
Smart Home Diagnostic (Lukas): Maytag
Maytag Account Lockout Fix: Troubleshooting Guide
#Maytag #Unknown #AccountLockout
🔍 Full Report: https://www.digitalhomefaults.org/maytag/unknown/maytag-account-lockout-fix
@chazh : I never said "passkeys are bull shit" (see https://todon.nl/@ErikvanStraten/115656347170869180).
🚨 Android, unfixed: https://seclists.org/fulldisclosure/2024/Feb/15
🚨 iOS/iPadOS (including 26.x): either
• if no fingerprint is configured
OR
• a fingerprint is configured but, under "Setting"s ➡️ "Touch ID & Passcode": "Password Autofill" is off
then a thief of my iDevice can logon to https://account.apple.com and https://icloud.com using my Apple passkey *without* scanning ANY finger or entering ANY screen unlock code.
Apple: "This is expected behavior".
@soatok : this is *NOT* what makes passkeys resistant to most phishing attacks.
Don't get fooled by the snake oil regarding asymmetric cryptography.
What makes passkeys strong:
1️⃣ The *main* domain name must match
2️⃣ https is mandatory
3️⃣ The length and randomness of the pubkey in most cases exceeds what is permitted for a password
4️⃣ The pubkey is unique per account
What makes passkeys weak:
1️⃣ They do not prevent session cookie (1FA) theft
2️⃣ Android and iOS/iPadOS passkeys are extremely hard to back up outside of their ecosystems (vendor lock-in)
3️⃣ An attacker with access to your account may ADD their own passkey (it's pubkey) or REPLACE yours
4️⃣ Implementation bugs: Android passkeys easily lost and iOS/iPadOS passkeys may be used without local authentication
5️⃣ Misinformation by people who THINK that they understand how passkeys, WebAuthn and FIDO2 work
6️⃣ (edited to add 15:40 UTC): weak https website certificates (passkeys could mitigate this risk by including the https cert or a reliable hash of it - provided that the RP checks it. Unfortunately this will break "legitimate" TLS MitM's).
Zwakke 2FA/MFA werkt AVERECHTS
In https://www.security.nl/posting/912441/65-plussers+gebruiken+tweestapsverificatie+minder+vaak+dan+gemiddeld#posting912477 schreef ik eerder deze week:
❝
2FA (MFA) is ruk.
Laat de overheid een wachtwoordmanager adviseren die wél op domeinnamen checkt.
❞
(Dat laatste kan standaard onder Android, iOS en iPadOS - middels "AutoFill").
Op veler "verzoek" onderbouwde ik die stelling (niet voor de eerste keer) in https://www.security.nl/posting/912441/65-plussers+gebruiken+tweestapsverificatie+minder+vaak+dan+gemiddeld#posting912530.
En in https://www.security.nl/posting/912441/65-plussers+gebruiken+tweestapsverificatie+minder+vaak+dan+gemiddeld#posting912733 legde ik uit waarom online inloggen *lastig* veilig te krijgen is - wat je ook verzint (het blijven shared secrets).
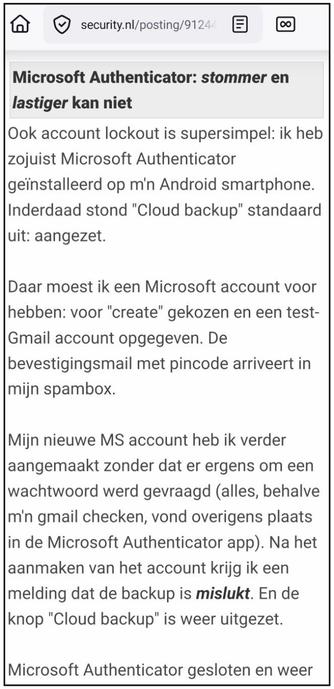
Vandaag heb ik Microsoft Authenticator ook maar weer eens getest (onder Android). Mijn bevindingen leest u in (de tweede helft van) https://www.security.nl/posting/912441/65-plussers+gebruiken+tweestapsverificatie+minder+vaak+dan+gemiddeld#posting912864 - hieronder een stukje daaruit.
#ZwakkeMFA #SMS #AuthenticatorApps #Zwakke2FA #Weak2FA #WeakMFA #MicrosoftAuthenticator #2FAsucks #MFAsucks #Phishing #NepWebsites #PhaaS #Evilginx2 #SIMswap #SS7 #AcountTakeOver #CookieTheft #AccountLockout
Fired Disney worker accused of hacking into restaurant menus, replacing them with Windings and false peanut allergy information
A disgruntled former Disney employee is facing charges that he hacked into the company's restaurant menu systems and wreaked havoc on its digital displays that could have potentially put lives at risk.