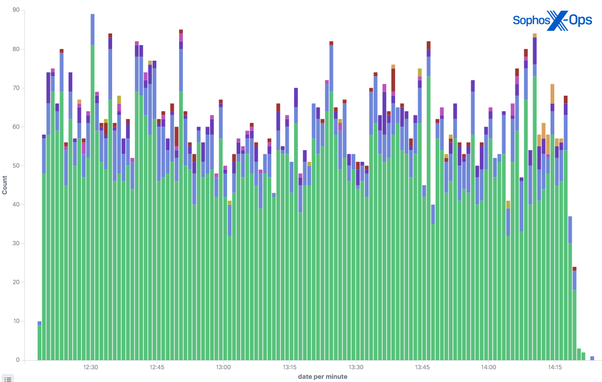
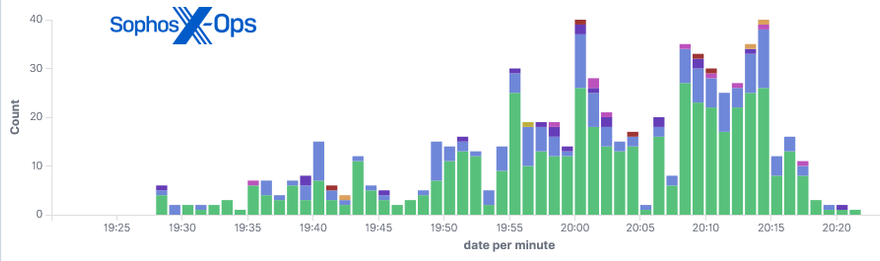
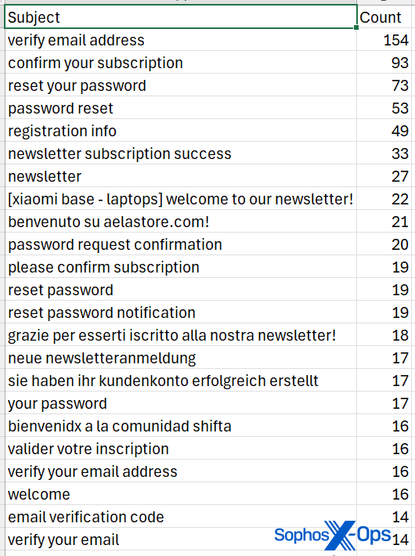
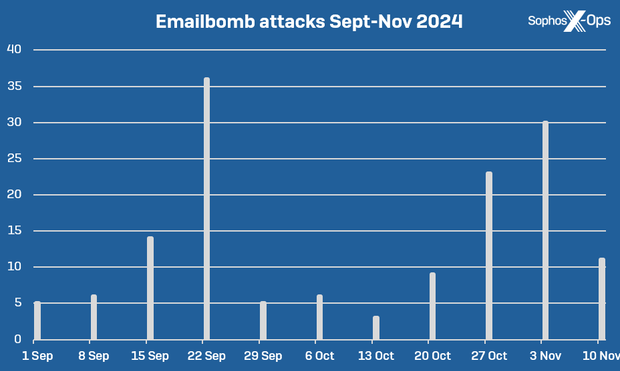
Since the beginning of September, Sophos X-Ops’ anti-spam research team has registered nearly 150 “emailbomb” attacks that targeted specific Sophos customers’ inboxes.
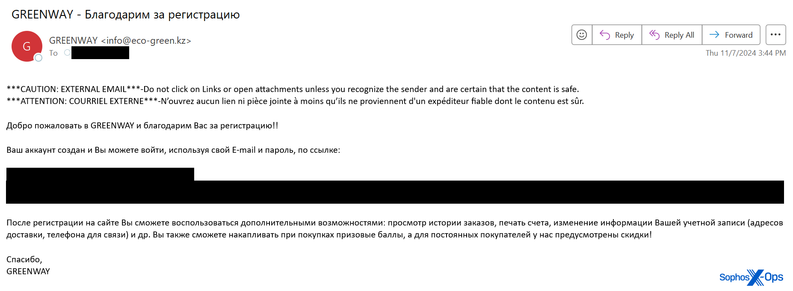
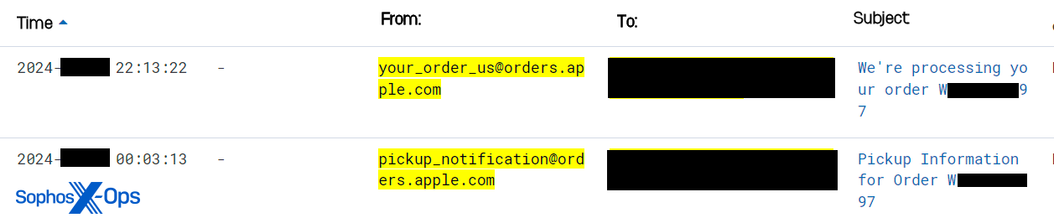
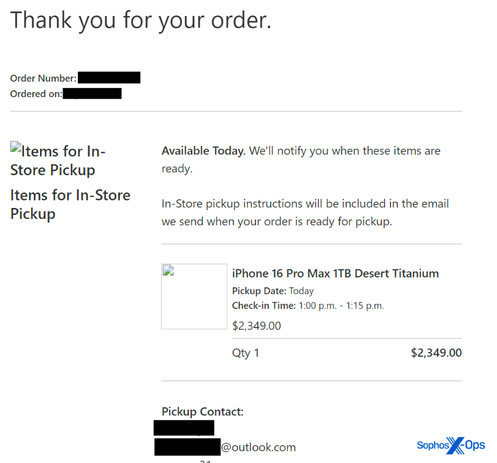
While similar, these are not spam attacks: threat actors use tools provided by otherwise benign websites to (un)/subscribe people to newsletters, and/or to help registered users self-manage an account with password resets.
The end result is the target's inbox becomes swamped with unexpected, benign email, sometimes for hours on end.
A 🧵