Boost VM security: 8 key strategies
Virtual machines have become ubiquitous in the enterprise by offering flexibility, scalability, and cost savings. But widespread adoption ...
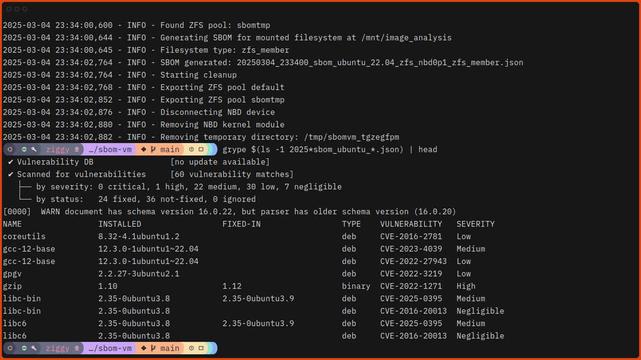
We're excited to share a new tool, sbom-vm, that simplifies VM security analysis. It addresses the challenges of generating SBOMs from virtual machines by directly working with disk images. Read the blog to learn how it works:
https://anchore.com/blog/making-virtual-machine-security-analysis-easier-with-sbom-vm/#SBOM #VMsecurity #Anchore
Making Virtual Machine Security Analysis Easier with sbom-vm
Discover sbom-vm, a new open-source tool that simplifies generating Software Bills of Materials (SBOMs) from virtual machine disk images by working outside the VM to overcome resource constraints and performance limitations.
Struggling to generate SBOMs from VMs? A new tool from
https://mastodon.social/@popey - sbom-vm, simplifies the process by working directly with VM disk images. Learn more:
https://anchore.com/blog/making-virtual-machine-security-analysis-easier-with-sbom-vm/#SBOM #VMsecurity #DevSecOps
Making Virtual Machine Security Analysis Easier with sbom-vm
Discover sbom-vm, a new open-source tool that simplifies generating Software Bills of Materials (SBOMs) from virtual machine disk images by working outside the VM to overcome resource constraints and performance limitations.
Heading to Seattle next week to present "Securing Confidential VMs with COCONUT-SVSM" at
#LinuxSecuritySummitNA! Excited to geek out about confidential computing!
#VMSecurity #ConfidentialComputingEnhancing your VM's security? Dive into our latest article, 'Maximizing VM Security,' to combat common threats like VM Escape and Sprawl. Ensure your virtual space remains breach-free! Read now:
https://zurl.co/a182 |
#VMware #VMSecurity #Virtualization #VMwareTips
Maximizing VM Security: How to Navigate and Neutralize VM Escape and Sprawl – Cyber Tips Guide
Discover essential strategies for VM protection, including the challenges of VM Escape and sprawl. Learn how to fortify your virtual environment effectively!