The slides for #TheSAS2019 "Dreambot business overview in 2019"
http://benkow.cc/DreambotSAS19.pdf
cc @[email protected]
Enjoy
So much cyber is going on at #TheSAS2019 https://t.co/3WXP3Fgjlx
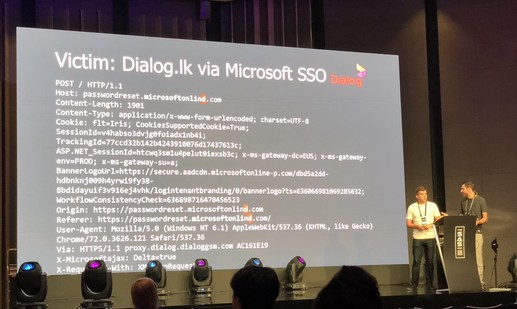
Bitflipping attacks are awesome and damn effective at scale. Passively collect credentials without any noise, talk by @bishopfox #TheSAS2019 https://t.co/WhdyS56fi5
Open-source offensive tools that end up in APT toolset, making it harder to track them. Talk by @JusticeRage and @felixaime #TheSAS2019 https://t.co/5bwx5nS1aE
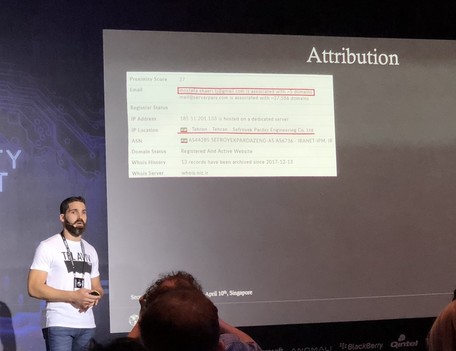
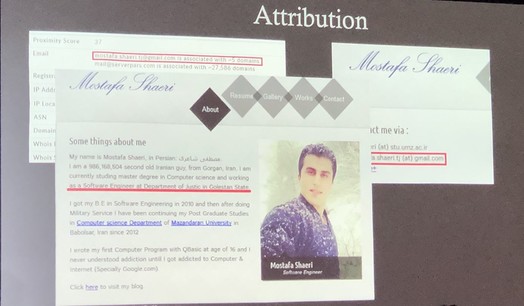
When attribution is easy! Malware targeting Israel from Iran, the developer was actually hosting the code on GitHub 🤦♂️ talk by @IdoNaor1 and @alexey_firsh #TheSAS2019 https://t.co/lC7cSZUp4T
New hot APT in the hood, looks highly sophisticated and stealthy AF, very interesting stuff https://securelist.com/project-tajmahal/90240/ #TheSAS2019
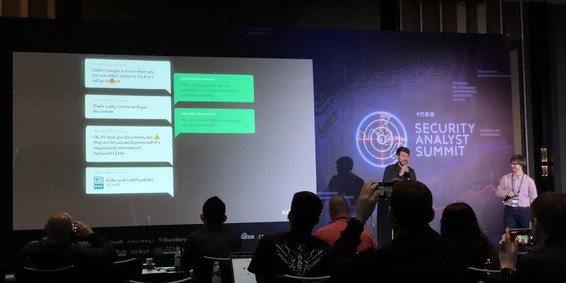
Some fine #FIN7 social engineering targeting customer support of their targets, talk by @felixaime and Yury Namestnikov #TheSAS2019 https://t.co/hCNndGwA0C
The botnets keep coming at #TheSAS2019 with @[email protected] & @[email protected] talking about #Dreambot #Gozi (now also on Mac OS X !)
Some casual cybercrime doxxing happening at #TheSAS2019 😳 https://t.co/Fx93nnvwDc
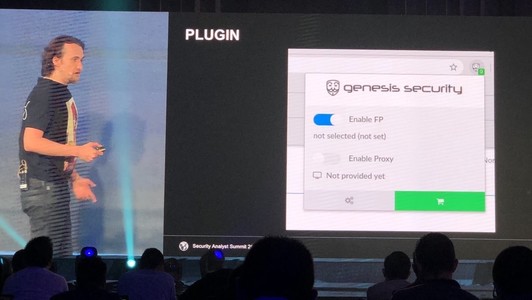
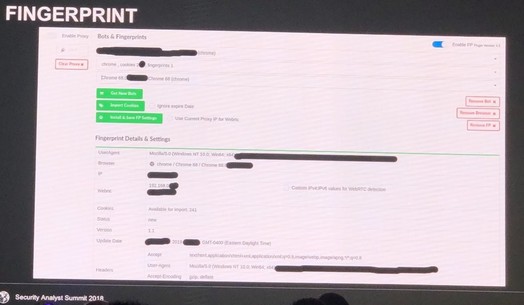
There’sa wide ecosystem for anti-fraud bypass, #carding is still alive and well. There’s even plugins to emulate the victims "fingerprints" (UA, IP, Cookies, etc.) - talk by @61ack1ynx #TheSAS2019 https://t.co/5VyBbEq37O