Question related to my previous post: is it possible to do some kind of static analysis on categorical code?
Or, what constraints should be imposed (or removed) on a category so that its code supports static analysis?
Question related to my previous post: is it possible to do some kind of static analysis on categorical code?
Or, what constraints should be imposed (or removed) on a category so that its code supports static analysis?
BOOTOSHI (@KingBootoshi)
Knip은 죽은 코드, 사용되지 않는 파일, unused export 등을 찾아내는 도구로, 에이전트가 grep 기반으로 코드베이스를 탐색할 때 발생하는 노이즈를 줄여준다. 에이전트의 코드 이해와 정리를 돕는 개발 도구로서 유용성이 강조되었다.
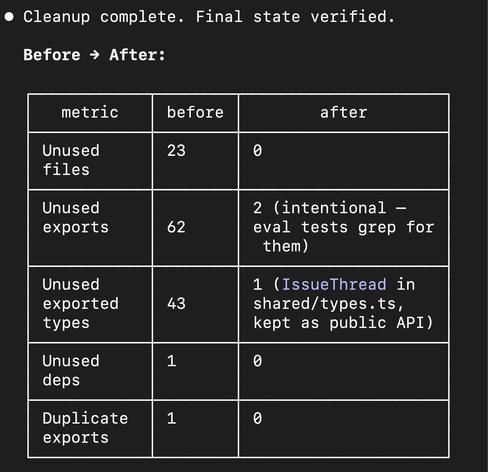
I LOVE KNIP WITH AGENTS knip is an app that finds dead code, dead files, unused exports etc bunch of noise that will affect your agents searching and understand the codebase via grep and possibly confuse them if you tell your agents to knip the codebase, it will find all dead
Recently, I made a stupid mistake that made me think about the way C++ APIs handle dependencies and what we can do to prevent dangling references and lifetime issues. 🤔
It was a surprisingly fun topic to explore that led me to the discovery of a very cool static analysis tool. Can you guess which one? 😎
You can find out in the article I wrote about the topic here:
➤ https://medium.com/@nerudaj/type-safe-dependency-management-in-c-a293703f00ff

REMnux v8 represents a structural modernization of a long-standing malware analysis distribution.
Technical highlights:
• Migration to Ubuntu 24.04 (modern kernel + LTS support)
• Cast-based installer replacing legacy CLI deployment
• AI-assisted workflows via MCP server
• Integration support for Ghidra with AI plugins
Tooling refresh includes:
YARA-X (Rust rewrite for performance improvements)
GoReSym (symbol recovery for Go binaries)
APKiD (Android packer detection)
Manalyze (PE/ELF/MachO static parsing)
This release signals an industry shift toward AI-augmented reverse engineering pipelines.
Is AI-assisted RE the new baseline for threat labs?
Source: https://cyberpress.org/remnux-v8-released/
Engage below.
Follow @technadu for deep technical cybersecurity updates.
#ThreatResearch #MalwareAnalysis #ReverseEngineering #YARAX #GoBinary #DFIR #Infosec #AIinSecurity #BlueTeam #StaticAnalysis #OpenSourceSecurity #SOC #ThreatHunting
How to Dominate SPFx Builds Using Heft
3,202 words, 17 minutes read time.
There comes a point in every developer’s career when the tools that once served him well start to feel like rusty shackles. You know the feeling. It’s 2:00 PM, you’ve got a deadline breathing down your neck, and you are staring at a blinking cursor in your terminal, waiting for gulp serve to finish compiling a simple change. It’s like trying to win a drag race while towing a boat. In the world of SharePoint Framework (SPFx) development, that sluggishness isn’t just an annoyance; it’s a direct insult to your craftsmanship. We need to talk about upgrading the engine under the hood. We need to talk about Heft.
The thesis here is simple: if you are serious about SharePoint development, if you want to move from being a tinkerer to a master builder, you need to understand and leverage Heft. It is the necessary evolution for developers who demand speed, precision, and scalability. This isn’t about chasing the shiny new toy; it’s about respecting your own time and the integrity of the code you ship.
In this deep dive, we are going to strip down the build process and look at three specific areas where Heft changes the game. First, we will look at the raw torque it provides through parallelism and caching—turning your build times from a coffee break into a blink. Second, we will discuss the discipline of code quality, showing how Heft integrates testing and linting not as afterthoughts, but as foundational pillars. Finally, we will talk about architecture and how Heft enables you to scale from a single web part to a massive, governed monorepo empire. But before we get into the nuts and bolts, let’s talk about why we are here.
For years, the SharePoint Framework relied heavily on a standard Gulp-based build chain. It worked. It got the job done. But it was like an old pickup truck—reliable enough for small hauling, but terrible if you needed to move a mountain. As TypeScript evolved, as our projects got larger, and as the complexity of the web stack increased, that old truck started to sputter. We started seeing memory leaks. We saw build times creep up from seconds to minutes.
The mental toll of a slow build is real. When you are in the flow state, holding a complex mental model of your application in your head, a thirty-second pause breaks your focus. It’s like dropping a heavy weight mid-set; getting it back up takes twice the energy. You lose your rhythm. You start checking emails or scrolling social media while the compiler chugs along. That is mediocrity creeping in.
Heft is Microsoft’s answer to this fatigue. Born from the Rush Stack family of tools, Heft is a specialized build system designed for TypeScript. It isn’t a general-purpose task runner like Gulp; it is a precision instrument built for the specific challenges of modern web development. It understands the graph of your dependencies. It understands that your time is the most expensive asset in the room.
We are going to explore how this tool stops the bleeding. We aren’t just going to look at configuration files; we are going to look at the philosophy of the build. This is for the guys who want to look at their terminal output and see green checkmarks flying by faster than they can read them. This is for the developers who take pride in the fact that their local environment is as rigorous as the production pipeline.
So, put on your hard hat and grab your wrench. We are about to tear down the old way of doing things and build something stronger, faster, and more resilient. We are going to look at how Heft provides the horsepower, the discipline, and the architectural blueprints you need to dominate your development cycle.
Unleashing Raw Torque through Parallelism and Caching
Let’s get straight to the point: speed is king. In the physical world, if you want to go faster, you add cylinders or you add a turbo. In the world of compilation, you add parallelism. The legacy build systems we grew up with were largely linear. Task A had to finish before Task B could start, even if they had absolutely nothing to do with each other. It’s like waiting for the paint to dry on the walls before you’re allowed to install the plumbing in the bathroom. It makes no sense, yet we accepted it for years.
Heft changes this dynamic by understanding the topology of your tasks. It utilizes a plugin architecture that allows different phases of the build to run concurrently where safe. When you invoke a build, Heft isn’t just mindlessly executing a list; it is orchestrating a symphony of processes. While your TypeScript is being transpiled, Heft can simultaneously be handling asset copying, SASS compilation, or linting tasks.
This is the difference between a single-lane country road and a multi-lane superhighway. By utilizing all the cores on your machine, Heft maximizes the hardware you paid for. Most of us are sitting on powerful rigs with 16 or 32 threads, yet we use build tools that limp along on a single thread. It’s like buying a Ferrari and never shifting out of first gear. Heft lets you open the throttle.
But parallelism is only half the equation. The real magic—the nitrous oxide in the tank—is caching. A smart developer knows that the fastest code is the code that never runs. If you haven’t changed a file, why are you recompiling it? Why are you re-linting it? Legacy tools often struggle with this, performing “clean” builds far too often just to be safe.
Heft implements a sophisticated incremental build system. It tracks the state of your input files and the configuration that governs them. When you run a build, Heft checks the signature of the files. If the signature matches the cache, it skips the work entirely. It retrieves the output from the cache and moves on.
Imagine you are working on a massive project with hundreds of components. You tweak the CSS in one button. In the old days, you might trigger a cascade of recompilation that took forty seconds. With Heft, the system recognizes that the TypeScript hasn’t changed. It recognizes that the unit tests for the logic haven’t been impacted. It only reprocesses the SASS and updates the bundle. The result? A build that finishes in milliseconds.
This speed changes how you work. It tightens the feedback loop. You make a change, you hit save, and the result is there. It encourages experimentation. When the penalty for failure is a thirty-second wait, you play it safe. You write less code because you dread the build. When the penalty is zero, you try new things. You iterate. You refine.
Furthermore, this caching mechanism isn’t just for your local machine. In advanced setups involving Rush (which we will touch on later), this cache can be shared. Imagine a scenario where a teammate fixes a bug in a core library. The CI server builds it and pushes the cache artifacts to the cloud. When you pull the latest code and run a build, your machine downloads the pre-built artifacts. You don’t even have to compile the code your buddy wrote. You just link it and go.
This is the raw torque we are talking about. It is the feeling of power you get when the tool works for you, not against you. It is the satisfaction of seeing a “Done in 1.24s” message on a project that used to take a minute. It respects the fact that you have work to do and limited time to do it. It clears the path so you can focus on the logic, the architecture, and the solution, rather than staring at a progress bar.
Enforcing Discipline with Rigorous Testing and Linting
Speed without control is just a crash waiting to happen. You can have the fastest car on the track, but if the steering wheel comes off in your hands at 200 MPH, you are dead. In software development, speed is the build time; control is quality assurance. This brings us to the second major usage of Heft: enforcing discipline through rigorous testing and linting.
Let’s be honest with each other. As men in this industry, we often have an ego about our code. We think we can write perfect logic on the first try. We think we don’t need tests because “I know how this works.” That is a rookie mindset. The expert knows that human memory is fallible. The expert knows that complexity grows exponentially. The expert demands a safety net.
Heft treats testing and linting not as optional plugins, but as first-class citizens of the build pipeline. In the legacy SPFx days, setting up Jest was a nightmare. You had to fight with Babel configurations, struggle with module resolution, and hack together scripts just to get a simple unit test to run. It was friction. And when something has high friction, we tend to avoid doing it.
Heft eliminates that friction. It comes with built-in support for Jest. It abstracts away the complex configuration required to get TypeScript and Jest playing nicely together. When you initialize a project with the proper Heft rig, testing is just there. You type heft test, and it runs. No drama, no configuration hell. Just results.
This ease of use removes the excuse for not testing. Now, you can adopt a Test-Driven Development (TDD) approach where you write the test before the code. You define the constraints of your battlefield before you send in the troops. This ensures that your logic is sound, your edge cases are covered, and your component actually does what the spec says it should do.
But Heft goes further than just running tests. It integrates ESLint deep into the build process. Linting is the drill sergeant of your code. It screams at you when you leave unused variables. It yells when you forget to type a return value. It forces you to adhere to a standard. Some developers find this annoying. They think, “I know what I meant, why does the computer care about a missing semicolon?”
The computer cares because consistency is the bedrock of maintainability. When you are working on a team, or even when you revisit your own code six months later, you need a standard structure. Heft ensures that the rules are followed every single time. It doesn’t let you get lazy. If you try to commit code that violates the linting rules, the build fails. The line stops.
This creates a culture of accountability. It forces you to address technical debt immediately rather than sweeping it under the rug. It changes the psychology of the developer. You stop looking for shortcuts and start taking pride in the cleanliness of your code. You start viewing the linter not as an enemy, but as a spotter in the gym—there to make sure your form is perfect so you don’t hurt yourself.
Moreover, Heft allows for the standardization of these rules across the entire organization. You can create a shared configuration rig. This means every project, every web part, and every library follows the exact same set of rules. It eliminates the “it works on my machine” arguments. It standardizes the definition of “done.”
When you combine the speed of Heft’s incremental builds with the rigor of its testing and linting integration, you get a development environment that is both fast and safe. You can refactor with confidence. You can tear out a chunk of legacy code and replace it, knowing that if you broke something, the test suite will catch it instantly. It turns coding from a game of Jenga into a structural engineering project. You are building on a foundation of reinforced concrete, not mud.
Architecting the Empire with Monorepo Scalability
Now we arrive at the third pillar: Scalability. Most developers start their journey building a single solution—a shed in the backyard. It has a few tools, a workbench, and a simple purpose. But as you grow, as your responsibilities increase, you aren’t just building sheds anymore. You are building skyscrapers. You are managing an empire of code.
In the SharePoint world, this usually manifests as a sprawling ecosystem of web parts, extensions, and shared libraries. You might have a library for your corporate branding, another for your data access layer, and another for common utilities. Then you have five different SPFx solutions that consume these libraries.
Managing this in separate repositories is a logistical nightmare. You fix a bug in the utility library, publish it to npm, go to the web part repo, update the version number, run npm install, and hope everything syncs up. It’s slow, it’s prone to version conflicts, and it kills productivity. This is “DLL Hell” reimagined for the JavaScript age.
Heft is designed to work hand-in-glove with Rush, the monorepo manager. This is where you separate the amateurs from the pros. A monorepo allows you to keep all your projects—libraries and consumers—in a single Git repository. But simply putting folders together isn’t enough; you need a toolchain that understands how to build them.
Heft provides that intelligence. When you are in a monorepo managed by Rush and built by Heft, the system understands the dependency tree. If you change code in the “Core Library,” and you run a build command, the system knows it needs to rebuild “Core Library” first, and then rebuild the “HR WebPart” that depends on it. It handles the linking automatically.
This symlinking capability is a game-changer. You are no longer installing your own libraries from a remote registry. You are linking to the live code on your disk. You can make a change in the library and see it reflected in the web part immediately. It tears down the walls between your projects.
But Heft contributes even more to this architecture through the concept of “Rigs.” In a large organization, you don’t want to copy and paste your tsconfig.json, eslintrc.js, and jest.config.js into fifty different project folders. That is a maintenance disaster waiting to happen. If you want to update a rule, you have to edit fifty files.
Heft Rigs allow you to define a standard configuration in a single package. Every other project in your monorepo then “extends” this rig. It’s like inheritance in object-oriented programming, but for build configurations. You define the blueprint once. If you decide to upgrade the TypeScript version or enable a stricter linting rule, you change it in the rig. Instantly, that change propagates to every project in your empire.
This is leadership through architecture. You are enforcing standards and simplifying maintenance without micromanaging every single folder. It allows you to onboard new developers faster. They don’t need to understand the intricacies of Webpack configuration; they just need to know how to consume the rig.
It also solves the problem of “phantom dependencies.” One of the plagues of npm is that packages often hoist dependencies to the top level, allowing your code to access libraries you never explicitly declared in your package.json. This works fine until it doesn’t—usually in production. Heft, particularly when paired with the Rush Stack philosophy using PNPM, enforces strict dependency resolution. If you didn’t list it, you can’t use it.
This might sound like extra work, but it is actually protection. It prevents your application from relying on accidental code. It ensures that your supply chain is clean. It is the digital equivalent of knowing exactly where every bolt and screw in your engine came from.
By embracing the Heft and Rush ecosystem, you are positioning yourself to handle complexity. You are saying, “I am not afraid of scale.” You are building a system that can grow from ten thousand lines of code to a million lines of code without collapsing under its own weight. This is the difference between building a sandcastle and building a fortress. One washes away with the tide; the other stands for centuries.
Conclusion
We have covered a lot of ground, but the takeaway is clear. The tools we choose define the limits of what we can create. If you stick with the default, out-of-the-box, legacy configurations, you will produce default, legacy results. You will be constrained by slow build times, you will be plagued by regression bugs, and you will drown in the complexity of dependency management.
Heft offers a different path. It offers a path of mastery.
We looked at how Heft provides the raw torque necessary to obliterate wait times. By utilizing parallelism and intelligent caching, it respects the value of your time. It keeps you in the flow, allowing you to iterate, experiment, and refine your work at the speed of thought. It’s the high-performance engine your development machine deserves.
We examined the discipline Heft brings to the table. By making testing and linting native, effortless parts of the workflow, it removes the friction of quality assurance. It turns the “chore” of testing into a standard operating procedure. It acts as the guardian of your code, ensuring that every line you commit is clean, consistent, and robust. It demands that you be a better programmer.
And finally, we explored the architectural power of Heft in a scalable environment. We saw how it acts as the cornerstone of a monorepo strategy, enabling you to manage vast ecosystems of code with the precision of a surgeon. Through rigs and strict dependency management, it allows you to govern your codebase with authority, ensuring that as your team grows, your foundation remains solid.
There is a certain grit required to make this switch. It requires you to step out of the comfort zone of “how we’ve always done it.” It requires you to learn new configurations and understand the deeper mechanics of the build chain. But that is what men in this field do. We don’t shy away from complexity; we conquer it. We don’t settle for tools that rust; we forge new ones.
So, here is the challenge: Take a look at your current SPFx project. Look at the gulpfile.js. Look at how long you spend waiting. Ask yourself if this is the best you can do. If the answer is no, then it’s time to pick up Heft. It’s time to stop tinkering and start engineering.
Call to Action
If this post sparked your creativity, don’t just scroll past. Join the community of makers and tinkerers—people turning ideas into reality with 3D printing. Subscribe for more 3D printing guides and projects, drop a comment sharing what you’re printing, or reach out and tell me about your latest project. Let’s build together.
D. Bryan King
Sources
Disclaimer:
The views and opinions expressed in this post are solely those of the author. The information provided is based on personal research, experience, and understanding of the subject matter at the time of writing. Readers should consult relevant experts or authorities for specific guidance related to their unique situations.
#assetCopying #automatedTesting #buildAutomation #buildCaching #buildOptimization #buildOrchestration #codeQuality #codingDiscipline #codingStandards #continuousIntegration #developerProductivity #devopsForSharePoint #enterpriseSoftwareDevelopment #ESLintConfiguration #fastBuildPipelines #fullStackDevelopment #GulpAlternative #HeftBuildSystem #incrementalBuilds #JavaScriptBuildTools #JestTestingSPFx #Microsoft365Development #microsoftEcosystem #modernWebStack #monorepoArchitecture #nodejsBuildPerformance #parallelCompilation #phantomDependencies #PNPMDependencies #programmerProductivity #rigConfiguration #rigorousLinting #rigorousTesting #RushMonorepo #RushStack #sassCompilation #scalableWebDevelopment #SharePointDevelopment #SharePointFramework #sharepointWebParts #softwareArchitecture #softwareCraftsmanship #softwareEngineering #SPFx #SPFxExtensions #SPFxPerformance #SPFxToolchain #staticAnalysis #strictDependencyManagement #taskRunner #TDDInSharePoint #technicalDebt #TypeScriptBuildTool #TypeScriptCompiler #TypeScriptOptimization #webPartDevelopment #webProgramming #webpackOptimization
Brakeman provides static analysis for Ruby on Rails by modeling data flow across application components and mapping results to known vulnerability patterns.
Its strength lies in early-stage visibility: identifying code-level issues, insecure configurations, and vulnerable dependencies before deployment. Support for baselining and result comparison helps teams manage findings over time.
From a security engineering perspective:
How do you measure the long-term value of static tools in mature Rails environments?
Source: https://www.helpnetsecurity.com/2026/01/26/brakeman-open-source-vulnerability-scanner-ruby-on-rails/
Join the discussion and follow @technadu for grounded AppSec coverage.
#ApplicationSecurity #StaticAnalysis #RailsSecurity #DevSecOps #Infosec #TechNadu
Cousot on Abstact Interpretation
What the fuck is PHPStan