A new #SpyNote report is out! 🚨 Dive into the tactics of this Android RAT campaign, from dynamic payload decryption to new obfuscation methods. Learn how threat actors are using deceptive Google Play Store clones to target users:
🤖 Android devices can be a major cybersecurity hazard for businesses. See how #ANYRUN helps detect #malicious files early, accelerate investigations, and improve threat response.
Analysis of #SalvadorStealer and #SpyNote inside👇
https://any.run/cybersecurity-blog/how-android-malware-targets-businesses/?utm_source=mastodon&utm_medium=post&utm_campaign=android_targets_business&utm_term=160725&utm_content=linktoblog
🚨 Newly Registered Domains Distributing SpyNote Malware
The latest DomainTools Investigations (DTI) analysis reveals that deceptive websites hosted on newly registered domains are being used to deliver the potent AndroidOS SpyNote malware. These sites mimic the Google Chrome install page on the Google Play Store to lure victims into downloading SpyNote, a powerful Android remote access trojan (RAT) used for surveillance, data exfiltration, and remote control.
🔍 Key Findings:
🔷Deceptive Techniques: Websites mimic popular app installation pages to trick users.
🔷Domain Patterns: Common patterns in domain registration and website structure.
🔷Language Indicators: Mix of English and Chinese-language delivery sites.
🔷Malware Capabilities: Extensive surveillance, data theft, and remote control functionalities.
SpyNote's sophisticated capabilities make it a significant threat to individuals and organizations. It can steal sensitive data, activate cameras and microphones, manipulate calls, and even remotely wipe or lock devices. The malware's persistence often requires a factory reset for complete removal.
Check out the full analysis here: https://dti.domaintools.com/newly-registered-domains-distributing-spynote-malware/?utm_source=Mastodon&utm_medium=Social&utm_campaign=SpyNote-GooglePlayStore
#SpyNote #Malware #ThreatIntelligence #CyberSecurity #InfoSec
Newly Registered Domains Distributing SpyNote Malware - DomainTools Investigations | DTI
Deceptive websites hosted on newly registered domains are being used to deliver AndroidOS SpyNote malware. These sites mimic the Google Chrome install page on the Google Play Store.
🌐 Campagne #Malware in Italia - Week 49
📞 #APK Bank
🕵️♂️ #SpyNote / #Antidot / #Irata / #DroidBot / #SmSSpy
✉️ Email Campaigns
💼 #Formbook: Preventivo
📦 #AgentTesla: Spedizione
📑 #Remcos: Fattura
💰 #GuLoader: Pagamento
🧾 #XWorm: Fattura
🐍 #SnakeKeyLogger: Bonifico
🔖 #Lokibot: Prezzo
©️ #Rhadamanthys: Copyright
📄 #VipKeyLoggerL: Documento
📢 Resta vigile! 🚨
📢 Campagne #Malware in Italia – Week 48
🔍 Minacce rilevate:
#Formbook – 💰 Prezzi e Ordini
#SpyNote / #Irata – 📱 APK Bank
#SnakeKeyLogger – 🤑 Acquisti
#AsyncRAT – ⛓️💥 Copyright
#XWorm – 🧾 Fattura
#VipKeyLogger – 🎁 Offerta
#AgentTesla – 🚚 Spedizione
📢 Campagne #Malware in Italia – Week 47
🔍 Minacce rilevate:
#SpyNote / #Irata – 📱 APK Bank
#Remcos – 💳 Pagamento Bancario
#XWorm – 🧾 Fattura
#VipKeyLogger – 🎁 Offerta
#SnakeKeyLogger – 📦 Ordine
#Vidar – 📩 Fattura via PEC
#Formbook – 💰 Prezzi
#AgentTesla – 🚚 Spedizione
#Lumma – ⚖️ Copyright
Campagne #Malware #Italy Week 41
☠️🔥💣👻
#SpyNote: APK Bank
#Formbook: Estratto Conto
#SnakeKeyLogger: Pagamento Swife
#AgentTesla: Booking
#Remcos: Richiesta Prezzi
#XWorm: Fattura Google
🚨 Nuova campagna di phishing bancario diffonde il #malware Android #EagleSpy!
Questa minaccia, simile a #CraxsRAT e #SpyNote, ruba dati sensibili dai dispositivi Android.
Scopri di più e proteggi il tuo smartphone!
👉 https://www.d3lab.net/nuova-campagna-di-phishing-diffonde-malware-android-eaglespy/
Nuova Campagna di Phishing diffonde malware Android EagleSpy
Una recente campagna di phishing sta diffondendo il malware Android EagleSpy, un potente RAT in grado di rubare dati sensibili attraverso false app bancarie. Analizziamo le somiglianze tecniche con SpyNote e CraxsRAT, rivelando le sofisticate tecniche di offuscamento e il coinvolgimento dello stesso
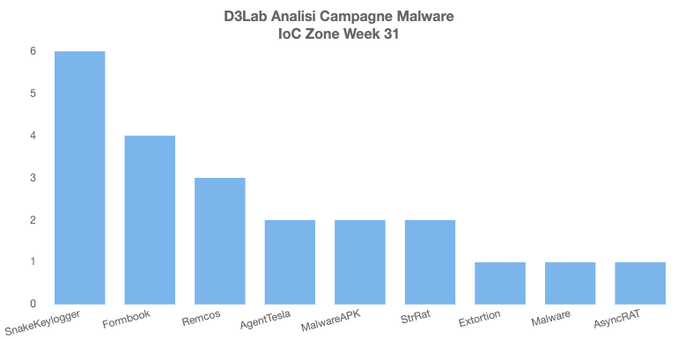
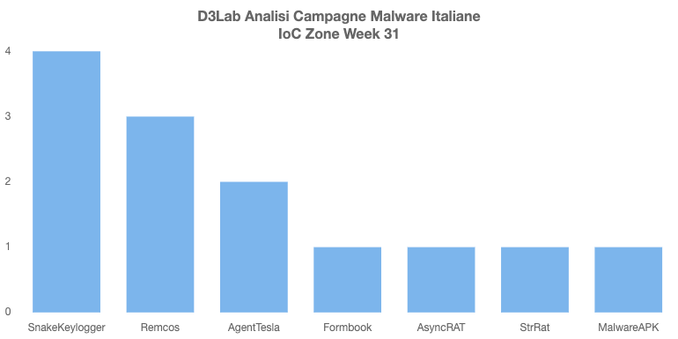
Campagne #Malware #Italy Week 31
👻🔥💣☠️
#SmokeLoader: Preventivo
#RemcosRAT: Pagamento Bancario
#AgentTesla: Etratto Conto
#Formbook: Ordine
#AsyncRAT: Fattura
#StrRAT: Delivery
#SpyNote - #BingoMod: Malware APK