Kazuar si evolve: Secret Blizzard (Turla) trasforma il suo backdoor storico in una botnet P2P modulare invisibile
Il gruppo russo Secret Blizzard (Turla/FSB) ha trasformato il malware Kazuar in una botnet peer-to-peer con tre moduli distinti (Kernel, Bridge, Worker) e 150 parametri di configurazione. La nuova architettura usa un sistema di elezione del leader per ridurre al minimo il traffico verso i server C2, rendendo il rilevamento estremamente difficile. Obiettivi: governi, ambasciate e settore difesa in Europa e Ucraina.Russian Hackers Upgrade Kazuar Backdoor to Modular Botnet
Microsoft researchers have uncovered a significant upgrade to the Kazuar backdoor, transforming it into a modular peer-to-peer botnet by the notorious Russian hacker group, Secret Blizzard. This sophisticated tool has been used to target high-stakes organizations and critical systems across Europe, Asia, and Ukraine.
#RussianHackers #KazuarBackdoor #ModularBotnet #SecretBlizzard #Turla
#KazuarBotnet #SecretBlizzard
https://www.microsoft.com/en-us/security/blog/2026/05/14/kazuar-anatomy-of-a-nation-state-botnet/

Kazuar: Anatomy of a nation-state botnet | Microsoft Security Blog
Kazuar, a sophisticated malware family attributed to the Russian state actor Secret Blizzard, has been under constant development for years and continues to evolve in support of espionage-focused operations. Over time, Kazuar has expanded from a relatively traditional backdoor into a highly modular peer-to-peer (P2P) botnet ecosystem designed to enable persistent, covert access to target environments.
https://www.databreachtoday.com/russia-uses-isps-to-spy-on-diplomats-warns-microsoft-a-29113 #SecretBlizzard #Turla
#SecretBlizzard
https://www.microsoft.com/en-us/security/blog/2025/07/31/frozen-in-transit-secret-blizzards-aitm-campaign-against-diplomats/
Frozen in transit: Secret Blizzard’s AiTM campaign against diplomats | Microsoft Security Blog
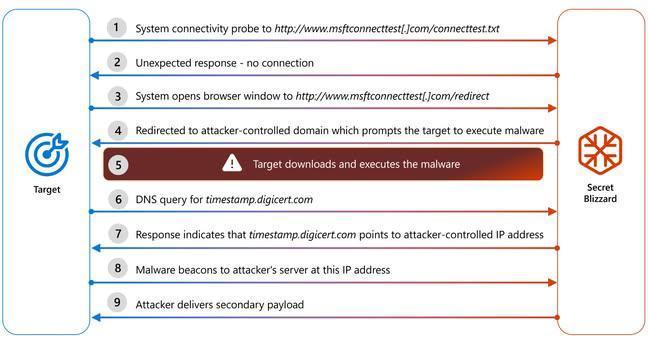
Microsoft Threat Intelligence has uncovered a cyberespionage campaign by the Russian state actor we track as Secret Blizzard that has been ongoing since at least 2024, targeting embassies in Moscow using an adversary-in-the-middle (AiTM) position to deploy their custom ApolloShadow malware.
Microsoft Threat Intelligence has uncovered a #CyberEspionage campaign by the #Russian state actor tracked as #SecretBlizzard that targets embassies located in Moscow using an AiTM position at the ISP level to deploy custom #ApolloShadow #malware.
The second part of the frequent freeloader blog series is out! MSTIC shares how Secret Blizzard abused tools of other threat actors to attack Ukraine.
#malware #cybersecurity #infosec #threatintelligence #microsoft #mstic #secretblizzard
Frequent freeloader part II: Russian actor Secret Blizzard using tools of other groups to attack Ukraine | Microsoft Security Blog
Since January 2024, Microsoft has observed Secret Blizzard using the tools or infrastructure of other threat groups to attack targets in Ukraine and download its custom backdoors Tavdig and KazuarV2.
#SecretBlizzard #Storm_1919 #Storm_1837
https://www.microsoft.com/en-us/security/blog/2024/12/11/frequent-freeloader-part-ii-russian-actor-secret-blizzard-using-tools-of-other-groups-to-attack-ukraine/
Frequent freeloader part II: Russian actor Secret Blizzard using tools of other groups to attack Ukraine | Microsoft Security Blog
Since January 2024, Microsoft has observed Secret Blizzard using the tools or infrastructure of other threat groups to attack targets in Ukraine and download its custom backdoors Tavdig and KazuarV2.
#UkraineRussiaWar️️ https://www.bleepingcomputer.com/news/security/russian-turla-hackers-hit-starlink-connected-devices-in-ukraine/