During the courses, students are taught to create viruses, videos using “manipulation, pressure, and hidden propaganda” and other skills relevant to the GRU, while the training materials draw on the GRU’s experience gained during the full-scale invasion of Ukraine.
3/3
Some of the graduates are already serving in GRU Unit 74455, which is responsible for attacks on civilian infrastructure in Ukraine and Georgia — which constitutes a war crime.
2/3
The Insider and its investigative partners have obtained documents from Department 4 of the Military Training Center at Bauman Moscow State Technical University that describe how the GRU trains students in hacking attacks & disinformation tactics.
🔗 https://theins.press/en/inv/292314
1/3

The GRU’s Hogwarts: Inside Bauman University’s Department 4, an elite spy school for Russian military intelligence
The Insider and its investigative partners have obtained documents from Department 4 of the Military Training Center at Bauman Moscow State Technical…
Silver Fox uses the new ABCDoor backdoor to target organizations in Russia and India
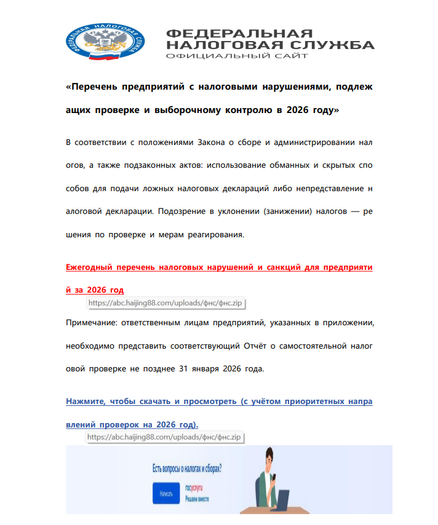
The Silver Fox group is targeting companies in Russia and India by impersonating tax authorities to distribute ValleyRAT and the new ABCDoor backdoor.
While primarily focused on targeting organizations in Taiwan, North America and Japan, the recent campaign is significant in that it shows the group expanding its regional focus for the first time to targets in Russia and India.
8/9
• Limited file-encryption features
• Self-updating and self-removal
• Collects extensive host metadata
However, it leaves forensic artifacts in the registry and `%LOCALAPPDATA%` directories that defenders can monitor for detection.
7/9
Then running under a legitimate `pythonw.exe` process to evade detection.
The malware focuses on covert remote interaction capabilities:
• Multi-monitor screen streaming via FFmpeg
• Remote mouse and keyboard control
• Clipboard theft
• File operations
6/9
`ABCDoor` establishes persistence through Windows Registry Run keys and scheduled tasks, then communicates with its command-and-control (C2) servers over HTTPS using asynchronous Socket[.]IO messaging.
5/9
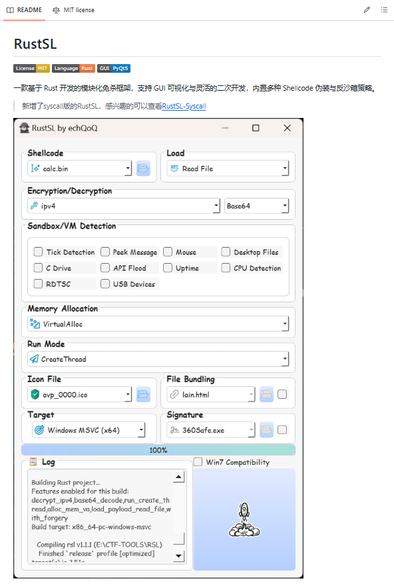
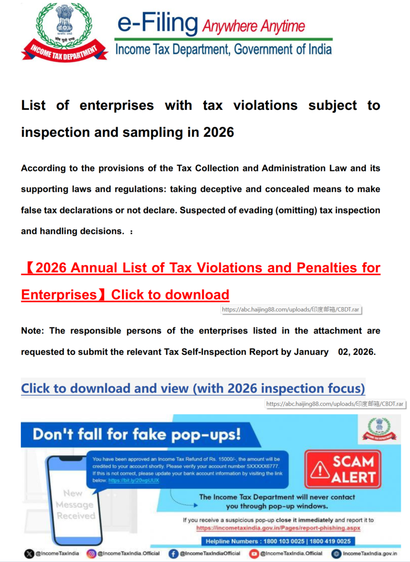
Once clicked `ABCDoor` gets unpacked and loaded into the host system. (With newer versions of `RustSL` expanding to include the geographic region of Japan.)
4/9
The starting point of the attack chain is a phishing email containing a PDF file, which features two clickable links a ZIP or RAR archive hosted on `abc.haijing88[.]com`.
3/9