AI-BOMs Emerge to Secure Enterprise AI Supply Chains
Imagine biting into a mysterious birthday cake without knowing its ingredients or who baked it - that's what it's like for enterprises trying to secure their AI supply chains without visibility into the components used to build their AI systems. Traditional software bills of materials just aren't cutting it in this new landscape.
#AiSupplyChains #ArtificialIntelligence #ShadowAi #Sbom #EnterpriseSecurity
El Reg has a story that exactly covers the problem I'm researching right now. It's not just the Devs, the whole company can be exposing secrets, corrupting data...
Supply chain attacks ↗️ 742% in 2023
Your traditional security stack wasn't built for this fight.
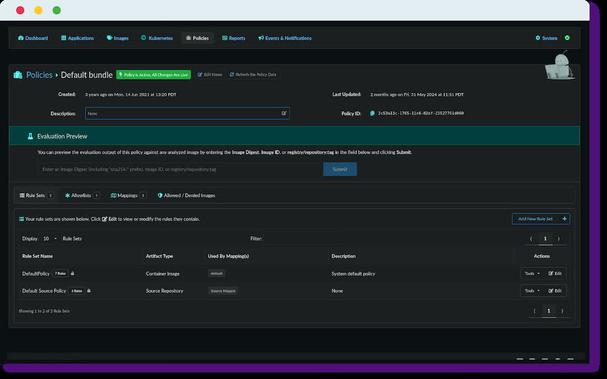
SBOM-first architecture changes everything ⚡
#Syft #SBOM #OpenSource
Shift-left compliance checking ⬅️
Catch violations before deployment, not during audits 🛡️
Security Tip: You can't patch what you don't know you have. 🛡️
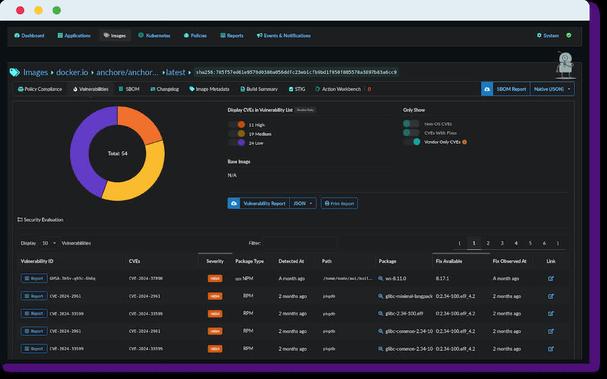
Implementing a Software Bill of Materials (SBOM) provides a machine-readable inventory of your software's ingredients. This is crucial for identifying vulnerable dependencies quickly when new CVEs are announced.
Use tools like Syft or Grype to automate this process. Track emerging threats at https://cvedatabase.com #CyberSecurity #SBOM #InfoSec #VulnerabilityManagement #CVE