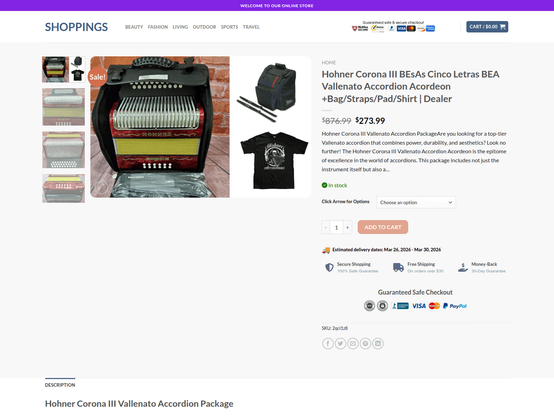
Dios mio! While researching a particular type of Colombian folk music, we stumbled across a .edu domain selling... accordions? Our first thought was potentially domain hijacking, but it appears to be more likely an exploitation of CVE-2026-27210 (TLDR; cross-site scripting). While the vulnerability has been patched in the plugin itself, not all pages have updated their plugins, and search engines have already indexed the poisoned pages! Pivoting led to 50+ additional domains found spread across three risky TLDs: .sbs, .pics, and .shop. The domains on .sbs and .pics appear to be config servers to exploit the vulnerability; the domains on .shop are the landing pages where victims can be scammed.
IOCs:
000o[.]sbs,0pen[.]sbs,123buys[.]shop,123me[.]shop,1bg[.]pics,1ki[.]pics,1mage[.]sbs,1ql[.]pics,1ty[.]pics,1vi[.]pics,1wr[.]pics,2ty[.]pics,569oagri[.]shop,66buys[.]shop,6ip[.]pics,6ym[.]pics,7rt[.]pics,8pi[.]pics,99buys[.]shop,99i[.]pics,9gwe[.]shop,a25n[.]shop,bk2[.]pics,bk59t[.]shop,buysok[.]shop,c68k[.]shop,cc1[.]pics,doo[.]pics,ep7[.]pics,estore-1[.]com,g9gvv[.]sbs,gaer896[.]shop,gm5[.]pics,gosok[.]shop,gt3[.]pics,h66p[.]shop,hh6[.]pics,iilvw[.]sbs,im9[.]pics,img1[.]sbs,in6[.]pics,jj3[.]pics,kk9[.]pics,lilil[.]sbs,llvvw[.]sbs,m66p6[.]shop,mebuys[.]shop,mg6[.]pics,mh8f6k[.]shop,mkk[.]pics,ms1[.]pics,nn6[.]pics,onsgs[.]com,p6[.]pics,p888p[.]shop,pan1[.]top,pic1[.]sbs,pic2[.]sbs,pt11[.]sbs,py3y[.]com,qq1[.]pics,rey89p[.]shop,shop56[.]shop,t88t8[.]shop,tp1[.]pics,tp9[.]pics,trues[.]sbs,up9[.]pics,upimg[.]sbs,uu2[.]pics,vt5[.]pics,vteyu[.]shop,vvf1[.]sbs,vvp1[.]sbs,w2w[.]pics,w88p[.]shop,wp59q[.]shop,wvlll[.]sbs,wvv1[.]sbs,wvvvv[.]sbs,x2p[.]pics,xyaer548[.]shop,yi1[.]pics
#dns #threatintel #threatintelligence #cybercrime #cybersecurity #infosec #infoblox #infobloxthreatintel #scam #seo_poisoning #seopoisoning