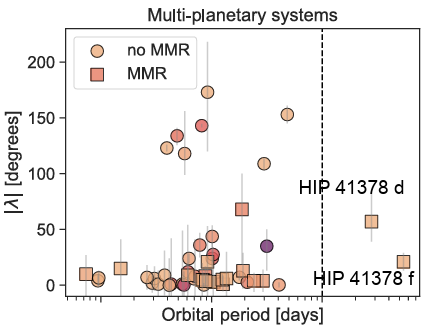
This is the spectroscopic transit of a #planet with an orbital period of 1.5 YEARS !! #HIP41378 🪐
In case you missed the great paper led by @sgrouffal (#ProudAdvisor), arXived over the summer, here is a recap'.
The planet HIP41378 f is a Saturn-sized transiting planet with an orbital period of 542 days. It means we can observe its transit only once every 1.5 years - it's actually once every 3 years from the ground as the host star is too close to the Sun (as seen from the Earth) every other transits.
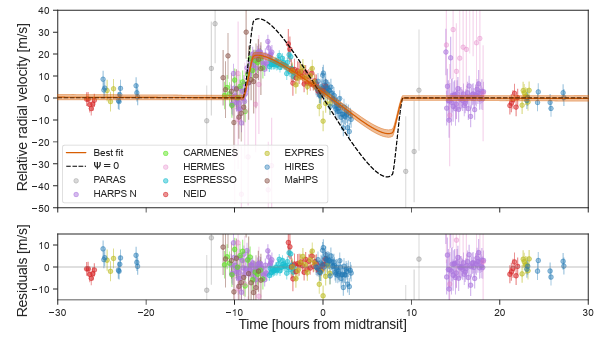
With such a long orbital period and a nearly circular orbit, the transit event lasts 19 hours (!). Hence, from the ground, any observer could only observe a tiny fraction of the transit. To overcome this issue, back in 2022, we set up a worldwide collaboration of almost all high-resolution radial-velocity spectrographs across the globe. Over the same night, all the instruments observed the target HIP41378 at the time of planet'f transit, allowing us to detect the Rossiter-McLaughlin (RM) effect.
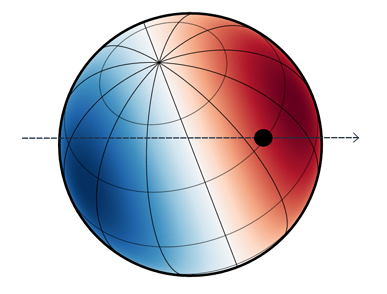
The RM effect is measuring the planet's orbital obliquity, i.e. the angle between the orbital plane and the spin axis of the star. While this angle is ~0º in the solar system, for HIP41378 it reaches Ψ=~52º.
[1/2]
#Science #Space #Exoplanet #Astrophysics #Astronomy #telescope
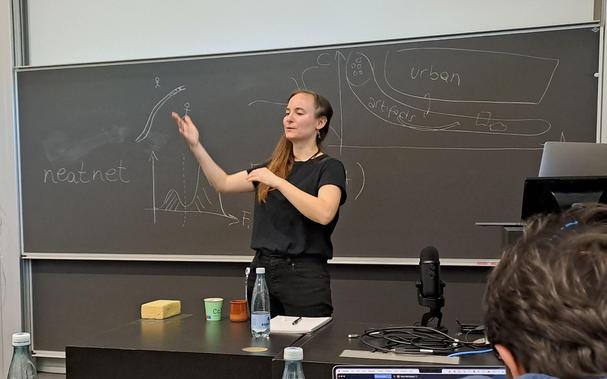
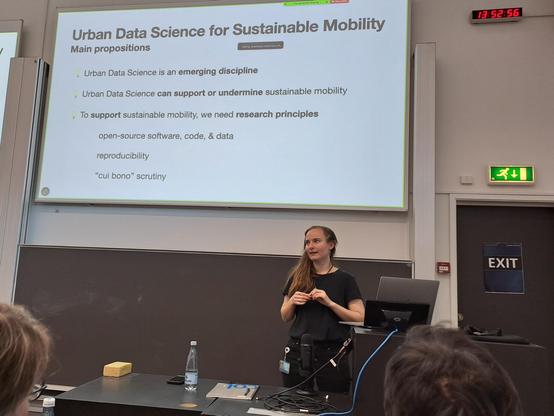
Thesis: https://en.itu.dk/Research/PhD-Programme/PhD-Defences/PhD-Defences-2025/March/Anastassia-Vybornova
As we welcome 2025, I'd like to take a moment to reflect on what an extraordinary year 2024 has been for Brown CS Secure Systems Lab (https://gitlab.com/brown-ssl/). It has been a year of innovation, creativity, and growth—both for the lab and for me personally as its director. Witnessing the passion, dedication, and brilliance of our team—Neophytos Christou, Alexander Gaidis, Marius Momeu, @dijin, and Vaggelis Atlidakis—has been truly fulfilling and inspiring!
In 2024, we tackled complex challenges and made significant strides in advancing our research on software hardening and OS kernel protection. Here are some highlights from this remarkable year:
✳️ Marius Momeu presented #SafeSlab at @acm_ccs #CCS2024. Safeslab hardens the Linux SLUB allocator against exploits that abuse use-after-free (#UaF) vulnerabilities, using #Intel #MPK. (Joint work with Technical University of Munich and @mikepo.)
📄 https://cs.brown.edu/~vpk/papers/safeslab.ccs24.pdf
💾 https://github.com/tum-itsec/safeslab
✳️ Neophytos Christou presented #Eclipse at @acm_ccs #CCS2024. Eclipse is a compiler-assisted framework that propagates artificial data dependencies onto sensitive data, preventing the CPU from using attacker-controlled input during speculative execution.
📄 https://cs.brown.edu/~vpk/papers/eclipse.ccs24.pdf
💾 https://gitlab.com/brown-ssl/eclipse
✳️ Di Jin presented #BeeBox at the @usenixassociation Security Symposium 2024. BeeBox hardens #Linux BPF/eBPF against transient execution attacks. #usesec24
📄 https://cs.brown.edu/~vpk/papers/beebox.sec24.pdf
💾 https://gitlab.com/brown-ssl/beebox
✳️ Yaniv David presented #Quack at the NDSS Symposium 2024. Quack hardens PHP code against deserialization attacks using a novel (static) duck typing-based approach. (Joint work with Andreas D Kellas and Junfeng Yang.) #NDSSsymposium2024
📄 https://cs.brown.edu/~vpk/papers/quack.ndss24.pdf
💾 https://github.com/columbia/quack
✳️ Marius Momeu presented #ISLAB at @ACM #ASIACCS24. ISLAB hardens SLAB-based (kernel) allocators, against memory errors, via SMAP-assisted isolation. (Joint work with Technical University of Munich and @mikepo.) #asiaccs
📄 https://cs.brown.edu/~vpk/papers/islab.asiaccs24.pdf
💾 https://github.com/tum-itsec/islab
🏆 #EPF (presented by Di Jin at @usenixassociation #ATC 2023) was the runner-up for the "Bug of the Year" award ("Weirdest Machine" category) at IEEE Symposium on Security and Privacy LangSec (Language-Theoretic Security) workshop 2024! #atc23 #LangSec
⌨️ https://langsec.org/spw24/bugs-of-the-year-awards.html
📄 https://cs.brown.edu/~vpk/papers/epf.atc23.pdf
💾 https://gitlab.com/brown-ssl/epf
🏅 I am honored and delighted to have received the "Distinguished Reviewer Award" at @acm_ccs #CCS2024!
🏅Alexander Gaidis has been awarded the "Distinguished Artifact Reviewer" award at the @usenixassociation Security Symposium 2024!
https://cs.brown.edu/news/2024/09/20/brown-cs-phd-student-alexander-j-gaidis-has-been-named-a-usenix-security-2024-distinguished-artifact-reviewer/
#usesec24 #proudadvisor
📢 I had the great pleasure of discussing some of these works recently at the Computer Systems Seminar at Boston University!
📽️ https://www.bu.edu/rhcollab/events/bu-systems-bu%E2%99%BAs-seminar/