Confused about AppSec vs. ProdSec? 🤔 This short dives into the differences – from secure coding to DevSecOps automation. Figure out which path is right for you! Check it out 💻 #AppSec #ProdSec #Cybersecurity
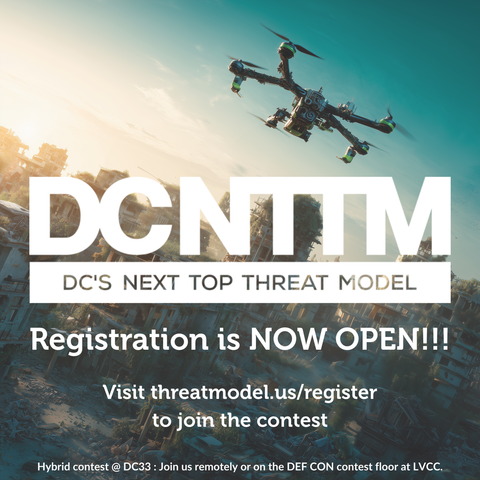
Registration is open for DC's Next Top Threat Model at @defcon 33. Visit https://threatmodel.us to learn more about our contest and register.
#DEFCON #DEFCON33 #DC33 #AppSec #InfoSec #ProdSec #ThreatModeling
It's that time of the year: Global Accessibility Awareness Day. Have you ever felt that you don't need accessibility features or any accommodations? We need to increase awareness on what these actually mean and why they make everyone's lives better!
Let's take an example. Are you wearing any visual aids like glasses or contact lenses? How about a temporary eyepatch after a surgery? Or maybe sunglasses to protect your eyes and help your sight when circumstances are not ideal? What about using reduced blue light and dark mode when you're struggling with headaches?
All of these are accommodations to meet accessibility needs. No matter if continuous, temporary or situational. There are tons more for you to go and find out about!
Let's stay curious for each other's needs, and that includes our own needs as well.
#GlobalAccessibilityAwarenessDay #accessibility #a11y #inclusion #osco #osco25 #CyberSecurity #Security #InfoSec #AppSec #ProdSec #OTsecurity [lisi]
Currently trying to learn hacking techniques to better understand it all
Taking Bazzite, there is no branch security, no approvals required, automatic releases with signing done for main and testing branches.
Taking ucore, there is no approvals required for PRs and many of the contributors merge without approval.
Likely more with other repos too but haven't looked further. Holy heck.
I'm not a huge #prodsec person to ensure secure releases, but this seems like a huge red flag to me if all it takes to get a release into people's machines is one compromised account.
Here's hoping I'm just super off about the whole thing and the security is actually good. But from an outside perspective I just feel scared using ublue atm.
Opened a ticket here as I don't have an account in their forums
github.com/ublue-os/bazzite/issues/1290
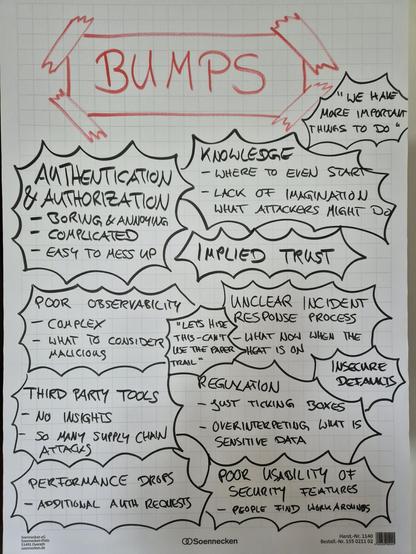
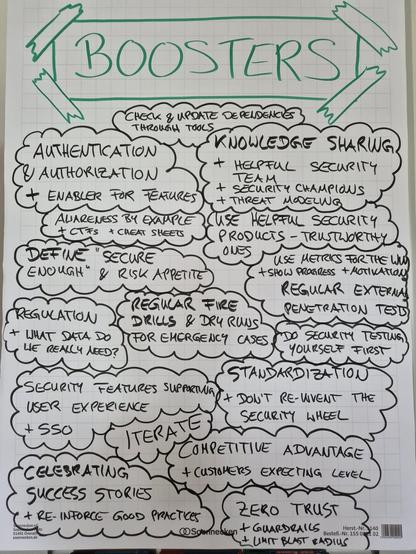
Hey all, I want to start to discuss more internal appsec/prodsec teams subjects, challenges and how to build a good programs. Anyone interested ?
And who should I follow for similar space?
We start our afternoon talks with Don McKeown talking about maturing #securedevelopment lifecyle, Gautam Peri showing us the art of #authbypass and Chris Smith discuss about #securityatspeed with Discord's #prodsec program. Check out all of this at OWASP BASC 2024.
Listen to Chris Smith talk about Discord's #prodsec program and how they managed #securityatspeed . This and many more exciting talks! Register at www.basconf.org
2024 BASC
The Boston Application Security Conference (BASC) is an annual conference held by the Boston chapter of the Open Web Application Security Project (OWASP) that includes presenters and workshops focused on current trends in application security. OWASP® is a nonprofit foundation that works to improve