That's a wrap on Pwn2Own Berlin 2026! 🏆 $1,298,250 awarded. 47 unique 0-days. 3 days of absolute chaos. And talk about main character energy - congrats to DEVCORE for claiming Master of Pwn with 50.5 points and $505,000 - they never slowed down. See you next year! #Pwn2Own #P2OBerlin
Collision! While Byung Young Yi (@yibarrack) of Out Of Bounds successfully demonstrated their exploit of Anthropic Claude Code, the bug used had been previously disclosed. They still earn $20,000 and 2 Master of Pwn points. #Pwn2Own #P2OBerlin
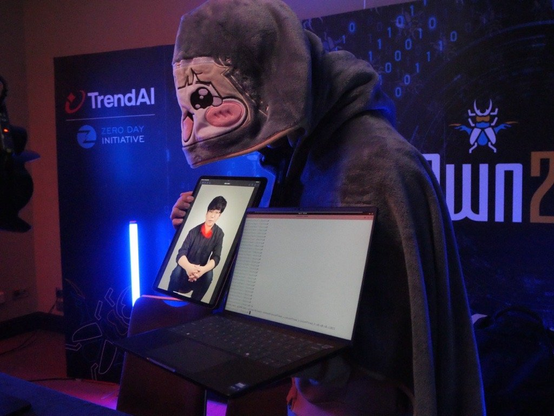
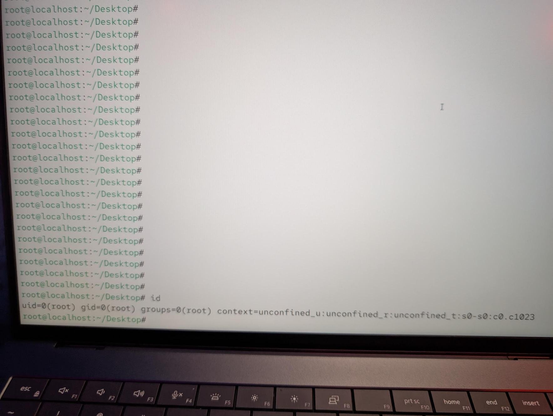
Mind blown alert 🤯! Nguyen Hoang Thach (@hi_im_d4rkn3ss) of STARLabs SG (@starlabs_sg) used a Memory Corruption bug to exploit VMware ESXi with the Cross-tenant Code Execution add-on, earning a sweeeeeet $200,000 and 20 Master of Pwn points. Full win let's go! #Pwn2Own #P2OBerlin
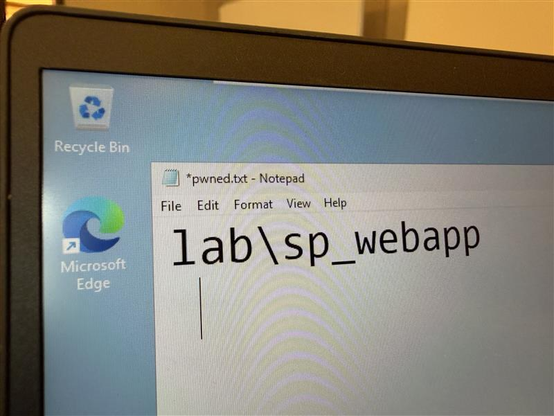
Booyah it's been confirmed! 🎉 splitline (@_splitline_) of DEVCORE Research Team chained 2 bugs to exploit Microsoft SharePoint, earning $100,000 and 10 Master of Pwn points. Massive aura farming this year at #P2OBerlin. Full win! #Pwn2Own
Wow what a fun way to wrap up the day! With TWO minutes to spare, Byung Young Yi (@yibarrack) of Out Of Bounds was able to exploit Anthropic Claude Code! If confirmed, they win $40,000 and 4 Master of Pwn points. They're off to the disclosure room to explain how they did it. #Pwn2Own #P2OBerlin
MASSIVE AURA POINTS! Nguyen Hoang Thach (@hi_im_d4rkn3ss) of STARLabs SG was able to exploit VMware ESXi! If confirmed, they win $200,000 and 20 Master of Pwn points. They're off to the disclosure room to explain how they did it and seal the deal. #Pwn2Own #P2OBerlin
ATE AND LEFT NO CRUMBS! splitline (@_splitline_) of DEVCORE Research Team totally cooked and was able to exploit Microsoft SharePoint! If confirmed, they win $100,000 and 10 Master of Pwn points. They're skeddadling off to the disclosure room now to drop the lore. #Pwn2Own #P2OBerlin
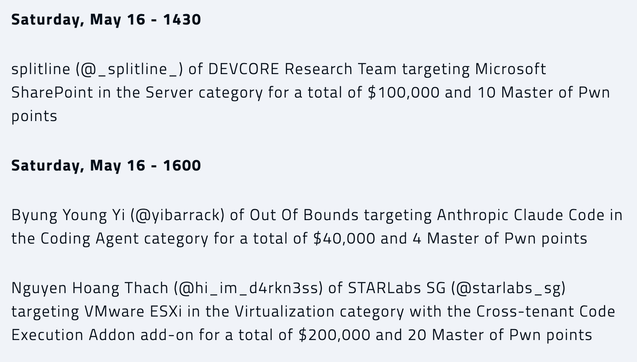
The math is mathing and we are on the brink of a million dollars! Here's the last set of attempts for the day. Stay tuned or stay square #Pwn2Own #P2OBerlin
Confirmed! Hyunwoo Kim (@v4bel) chained a use-after-free and uninitialized memory bug to escalate privileges on Red Hat Enterprise Linux for Workstations in the fourth round, earning $5,000 and 2 Master of Pwn points. #Pwn2Own #P2OBerlin
Collision! Although successful on stage, Emanuele Barbeno, Cyrill Bannwart, Yves Bieri, Lukasz D., Urs Mueller (@compasssecurity) of Compass Security targeted Anthropic Claude Code, hitting a one-vulnerability collision with a previous attempt and earning $20,000 and 2 Master of Pwn points. #Pwn2Own #P2OBerlin