#resilience #comsec #onetimepad #vibecoding #buildroot #embedded #dfir #redteam #preparedness
#resilience #comsec #onetimepad #vibecoding #buildroot #embedded #dfir #redteam #preparedness
Burn After Reading: One-Time Pad Encryption Using Dice
One day, you may find yourself in the position of not trusting any of your apps or electronic devices, but still needing to send an encrypted message to someone. There are three (3) things you need to accomplish this:
Pen/cil
Paper (graph paper helps)
A random number generator (in this case, 10-sided dice
https://anarchistrrl.noblogs.org/post/2025/10/28/burn-after-reading-one-time-pad-encryption-using-dice/
#onetimepad #encryption
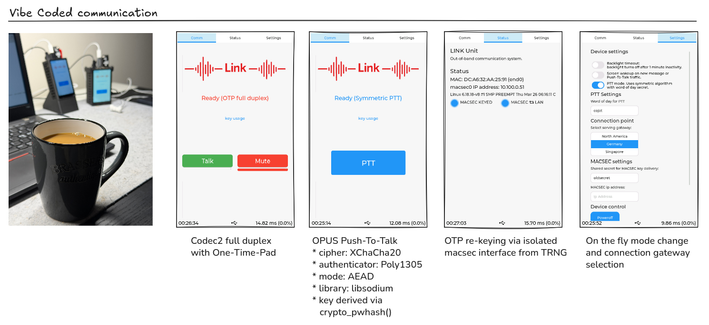
An interesting OTP chat implementation
#encryption #onetimepad #authentication #secrecy
https://app.radicle.xyz/nodes/ash.radicle.garden/rad%3Az9NtUTymSdxnuTcnzaM5qi7cuHPN
https://theblackchamber552383191.wordpress.com/2025/03/19/filler-ryan-mcbeth-otp-idea/
#filler #onetimepad
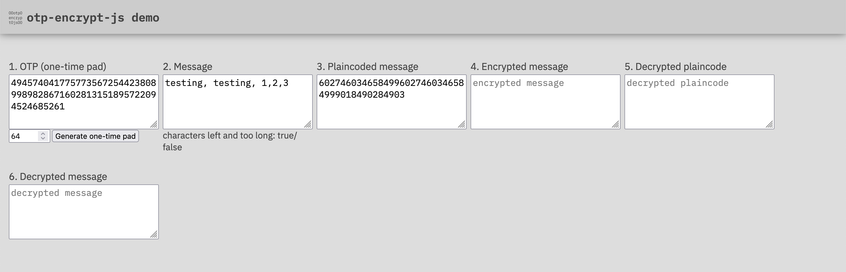
As far as I got today: plaincoding message text. And found a but in the otp-encrypt-js library. Can't plaincode unicode emojis. It'll be quick to fix.
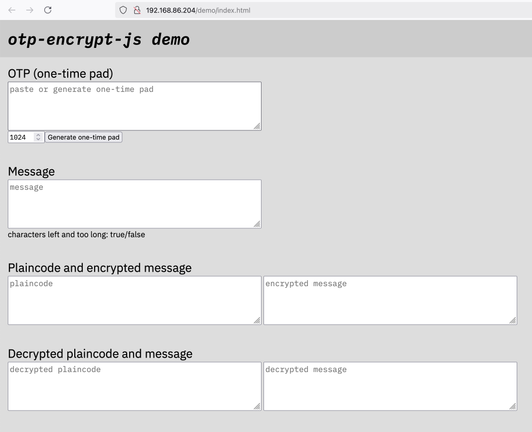
Demo for one-time encryption library, otp-encrypt-js, slowly shaping up!
#encrypt #otp #onetimepad #message #Javascript #browser
https://github.com/eklem/otp-encrypt-js
Gearing up for some more development on encrypting and decrypting messages for kids.
Just renamed my one-time pad encryptio library to something that was possible to remember:
otp-encryption-js
First thing is to make emojis unique over different versions of unicode emoji versions.
Then look at one-time pad exchange between phones.
#onetimepad #encryption #JavaScript #development #messaging #MessagingSecurity
I did not know it, so I did, what everybody shoud do; I did a quick research. Since there is little information on the internet, I consulted the orion website.
They state, that they are providing a #quantumcomputing secure chat solution, by using #onetimepad encryption. What they are not telling is how they solved the key generation and distribution.
#security #snakeoil #blockchain
WHO DID IT?
One of our information security “ancestors” invented the world’s only completely secure means of communication. And now we’re surrounded — night and day — by the “descendants” of that technology in new forms. It keeps our online transactions safe, and may have a renewed importance as we enter the quantum computing era.
We thought we knew who invented it, but history had a trick or two up its sleeve. It’s a bit like the mystery murder game, Clue.
➡️ Who?
➡️ What?
➡️ When?
➡️ Where?
➡️ Why?
➡️ How?
➡️ How Secure Was It?
➡️ Was It Commercially Successful?
➡️ What Was The Underlying Technology?
➡️ How Efficient Was Its Use? (always inefficient, or could it be massively efficient?)
Answers to all of these questions have been updated in the past 12 years.
Because of Frank Miller's implementation with a Telegraphic Code book, the use of a One-Time Pad could be, and often was, *outrageously* efficient, compared to the later use (with a cipher) which was painfully *inefficient.* This difference is only now becoming clear, since our understanding of who Frank Miller was and what he did is only about 12-13 years old.
The history of infosec got rewritten and we're all just trying to catch up.
I asked an infographic designer to create a comparison between our Old Understanding (invented in 1917) vs. our New Understanding (happened 35 years earlier, in 1882).
What do you think? Please feel free to offer your suggestions or thoughts to make this infographic more useful.
If you’d like to verify for yourself how efficient the use of a One-Time Pad could be, feel free to take this quick, 4-step challenge:
https://loistavainfosecurity.com/blog/f/one-time-pads-%E2%80%94-how-efficient-were-they
And the answer to the poll is . . . 1882!
Yup, it’s true. Asking someone to disclose their “mother’s maiden name” as a security technique was first publicly described in 1882.
That’s the year Sacramento, CA banker — Frank Miller — published his book titled "Telegraphic Code: To Insure Privacy and Secrecy In The Transmission Of Telegrams."
This was the same book which described the first concept and implementation of the One-Time Pad.
Frank and his fellow banker buddies conducted high finance over the Internet of their day, the Telegraph, which was considered by many to be completely insecure; about as private as sending a postcard.
How did you transfer loads of your employer’s money securely over an insecure means of communication?
You used a telegraphic code book and combined it with other layers of security. Big $$$$s were involved, and no one wanted — then or now — to be the one who screwed up a transaction.
So “mother’s maiden name” became one of the layers of security used in money transfers.
As they said on Battlestar Galactica: “All this has happened before, and all this will happen again.”
Interesting how things seem to repeat over and over.
Thanks to everyone who voted in the Poll!
#Infosec
#Cybersecurity
#MothersMaidenName
#InfosecTraining
#OneTimePad
 / Loistava
/ Loistava