Blocking all *.bc.googleusercontent.com on my mailserver as they send nothing but phishing mails and spam. Google doesn't really care about the 150+ reports I sent them, so on the blocklist they go.
Silly spammer "revenge". When you report spam in ways that it actually does something, some spammers get cranky about that and:
- Use a domain that is about to expire
- Use google mail for that domain
- set up a reflector e-mail address on that domain
- Run a script that spams hundreds of support systems of innocent websites
- Redirect the replies to those support tickets to my email address via google mail
Silly, but it seems to make the spammers happy.
Huh. It seems #Postfix in Debian trixie wrongly handles the "TLS-Required: No" header in mails, which in my case lead to mails getting strangely stuck in the local mail queue instead of going over the LMTP transport…
https://www.mail-archive.com/postfix-users@postfix.org/msg106677.html
Miraculously, mail servers that do not use/check neither SPF, DMARC nor DKIM still exist. This one from a consulting company in Hungary allowed me to track down the sender of spam using one of my mail accounts as spoofed `from:`. So, dear 1.202.53.77 from China, welcome to my blocklist :)
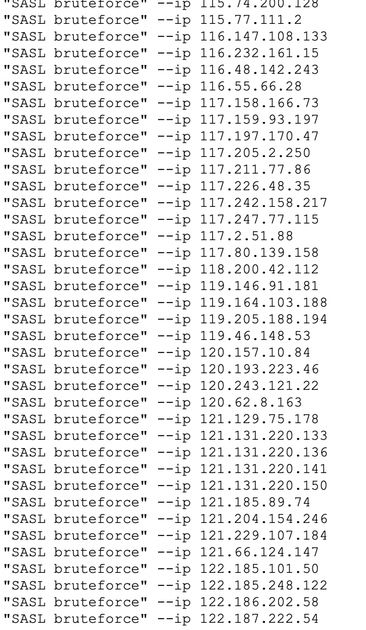
363 IP addresses in 24 hours, trying to guess user/password combinations on my mailserver. The botnets seem to be back in full force after a little over 2 weeks of almost nothing (yes, that coincides with the war against Iran).
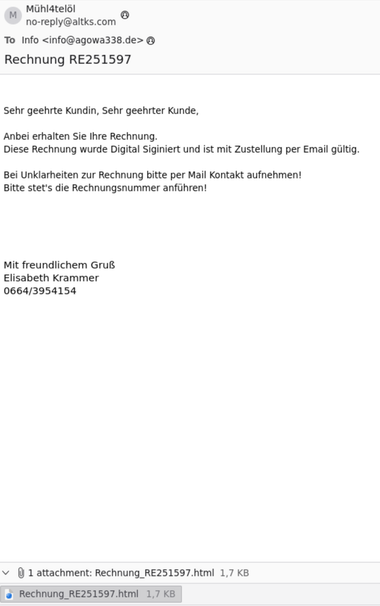
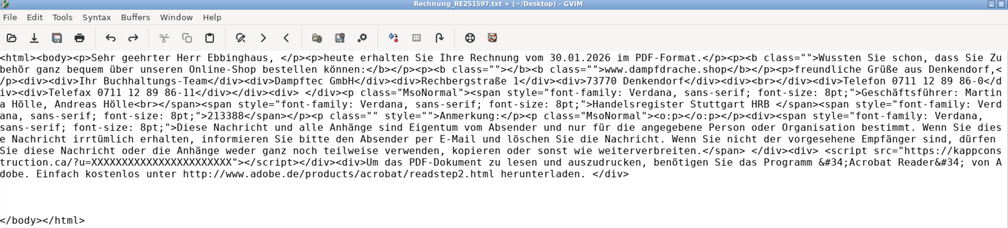
Honeypot mail account got a new kind of spam. Not seen attached .html files for years.
Are .html attachments in emails allowed by popular mail clients and webmailers again by now???
So I guess for the next few days you can send an e-mail to [email protected] and it will reach me ;)
I guess they will also use the support forms to try to subscribe me to whatever marketing stuff from there.
So I look forward to interesting messages from Bavarian restaurants, Austrian doctors and swiss lawyers :)
When spammers don't like you reporting their spam, they will:
- set up a forwarding email address on one of their servers with good DKIM/SPF/DMARC, typically on a domain that will expire soon
- Run a script that spams hundreds of support addresses/web forms with nonsense content using that forwarding address
- Forward all the confirmation receipts to your email address
That stuff is easy to block, but can be quite a nuisance to the affected support teams.
Well, it seems the botnets are coming back. After two weeks of almost nothing, today the SASL login attempts and support tickets opened using one of my email addresses are coming back. So. Back to business as usual. Report spammers and blocking these botnet IP adresses.