PSA for anyone using #QEMU #KVM for #SingleGPUPassthrough
Guides are all over the net suggesting hooks scripts invoking pci devices, unloading/loading kernel modules, and other unnecessary things. Here's my current hook script for starting the VM:
systemctl stop display-manager
That's it. And the reverse for teardown:
systemctl start display-manager
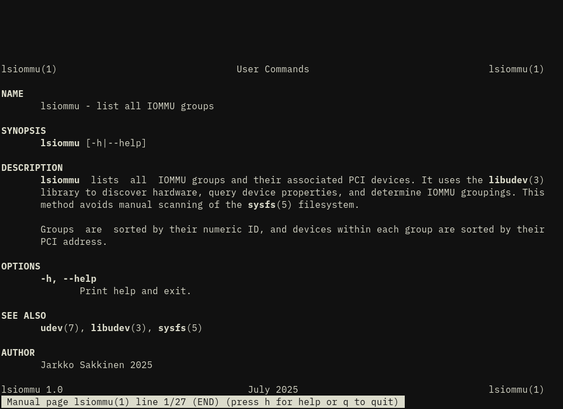
#IOMMU groups still apply, and you need to pass the correct PCI devices to your VM, but everything else is handled automatically.
Disclaimer that this is how it works currently for my AMD card. I did have a working setup with my NVIDIA card that did unload/load kernel modules, however it seems things have come a long way since I set that up.