Cisco Talos recently published an analysis of an EDR killer used by the #Qilin #ransomware gang. #ESETresearch tracks this threat as #CardSpaceKiller and we recently provided additional insights in our blog https://www.welivesecurity.com/en/eset-research/edr-killers-explained-beyond-the-drivers/
While we didn’t obtain direct evidence, we strongly believe that CardSpaceKiller is offered as a product on the darknet for reasons covered in the blog. We’ve detected it used by #Akira, #Medusa, and #MedusaLocker affiliates too.
The packer (identified as VX Crypt by Sophos) is not unique to this killer; it’s a PaaS used with other malware like #BumbleBee. But it is the single choice for the killer’s developer; unprotected samples were used only in 2025-02 https://www.sophos.com/en-us/blog/inside-shanya-a-packer-as-a-service-fueling-modern-attacks/
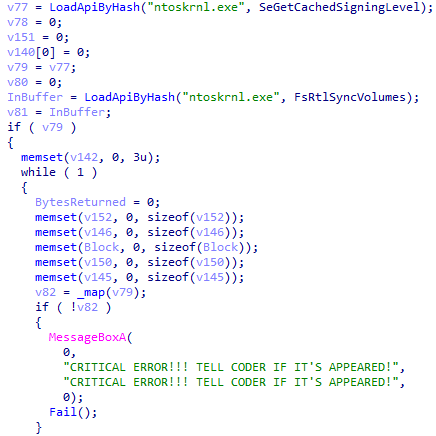
Beyond msimg32.dll mentioned in the Talos‘ blog, VX Crypt also names the payloads rtworkq.dll and version.dll, all abusing DLL side-loading for evasion. We’ve also observed an EXE variant in the wild, named 0th3r_av5.exe https://blog.talosintelligence.com/qilin-edr-killer/
Additional IoCs: 127B50C8185986A52AE66BF6E7E67A6FD787C4FC (version.dll)
22640D48F2E2A56C7A0708356B2B6990676B58B3 (version.dll)
3030DF03F36EC4C96B36B2E328FE3D7D9082811A (0th3r_av5.exe)
52D0358FF84295D231BC180CEDFDAF96631D67B4 (rtworkq.dll)
5D3CF785A440133A899412B800742716287D0B06 (msimg32.dll)
A3BDB419703A70157F2B7BD1DC2E4C9227DD9FE8 (0th3r_av5.exe)