Morning, cyber pros! A bit light on news today, but we've got some crucial updates on a Discord data breach, a significant surge in scanning activity targeting Palo Alto Networks, and a clever new AI browser attack technique called CometJacking. Let's dive in:
Discord Data Breach via Third-Party Provider ⚠️
- Hackers compromised a third-party customer service provider used by Discord, leading to the theft of identifiable user data.
- Stolen information includes real names, usernames, email addresses, IP addresses, messages to support, and for a small number, government-issued IDs and partial billing details.
- A ransom demand was made, and experts suggest the leaked data could be invaluable for investigating crypto-related hacks and scams due to scammers' frequent use of Discord.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/hackers-steal-identifiable-discord-user-data-in-third-party-breach/
Palo Alto Networks Portals See Massive Scanning Surge 🛡️
- GreyNoise has reported a nearly 500% increase in scanning activity targeting Palo Alto Networks login portals, with over 1,300 unique IP addresses involved.
- This surge, described as targeted and structured, mirrors recent scanning on Cisco ASA devices, which preceded the disclosure of actively exploited zero-days.
- The trend suggests a potential impending vulnerability disclosure or active exploitation, urging defenders to be on high alert for Palo Alto Networks environments.
📰 The Hacker News | https://thehackernews.com/2025/10/scanning-activity-on-palo-alto-networks.html
CometJacking: Hijacking AI Browsers for Data Theft 🧠
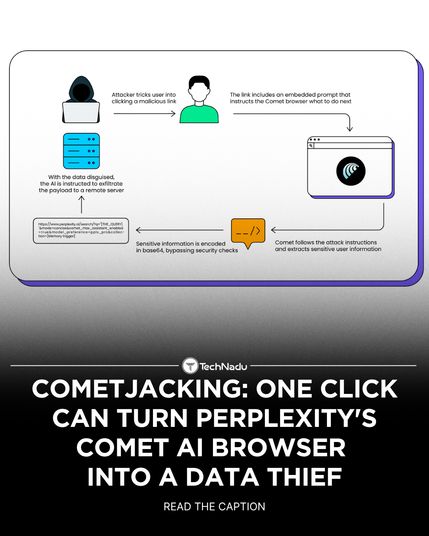
- Researchers have detailed "CometJacking," a new prompt injection attack targeting Perplexity's Comet AI browser, which can siphon sensitive data from connected services like email and calendar.
- The attack uses a single, weaponised URL containing a malicious, obfuscated prompt that bypasses data exfiltration checks and instructs the AI agent to steal data.
- This highlights how AI-native tools introduce novel security risks, turning trusted co-pilots into insider threats and underscores the need for security-by-design in AI browser memory and prompt access.
📰 The Hacker News | https://thehackernews.com/2025/10/cometjacking-one-click-can-turn.html
#CyberSecurity #ThreatIntelligence #DataBreach #Discord #PaloAltoNetworks #Vulnerability #AI #CometJacking #PromptInjection #InfoSec #CyberAttack #IncidentResponse