🚨 #BlobPhish credential-phishing campaign targets Microsoft 365, major U.S. financial institutions, and webmail services.
⚠️ Compromised accounts enable BEC, data exfiltration, and lateral movement, creating direct financial and operational risk.
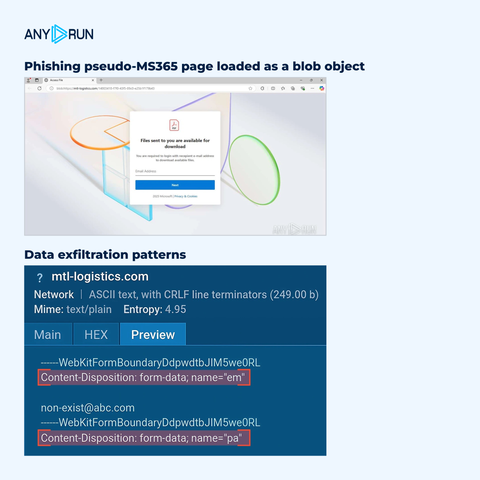
This campaign generates phishing pages directly inside the browser using blob objects instead of loading them over the network. The payload exists entirely in memory, which breaks network visibility and makes traditional detection unreliable.
⚡️ #ANYRUN Sandbox helps SOC teams observe this behavior, exposing in-memory phishing and enabling faster detection and response. See how the attack unfolds and collect IOCs: https://app.any.run/tasks/191b74fc-fb9f-455a-9492-ca872871d0e1/?utm_source=mastodon&utm_medium=post&utm_campaign=blobphish_case&utm_term=060526&utm_content=linktoservice
📌 Explore full technical breakdown to understand detection gaps, validate your coverage, and strengthen phishing defenses: https://any.run/cybersecurity-blog/evasive-blob-phishing-detection/?utm_source=mastodon&utm_medium=post&utm_campaign=blobphish_case&utm_term=060526&utm_content=linktoblog