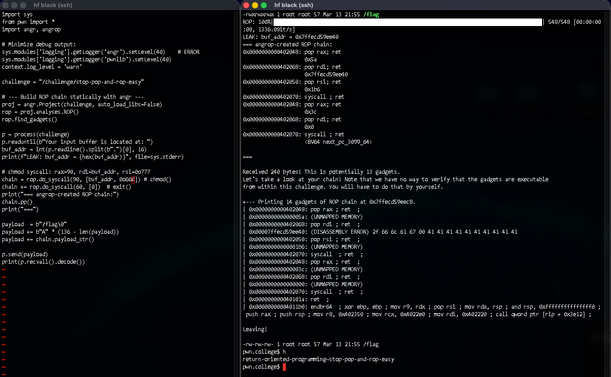
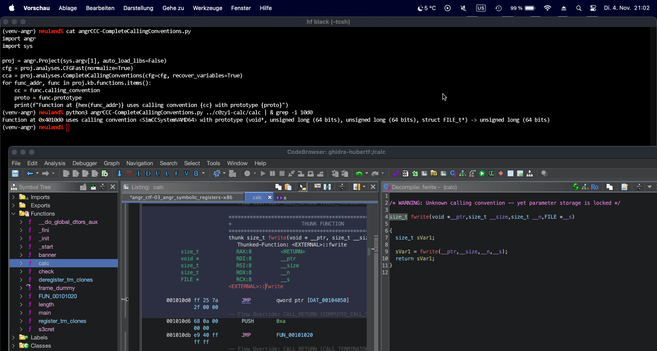
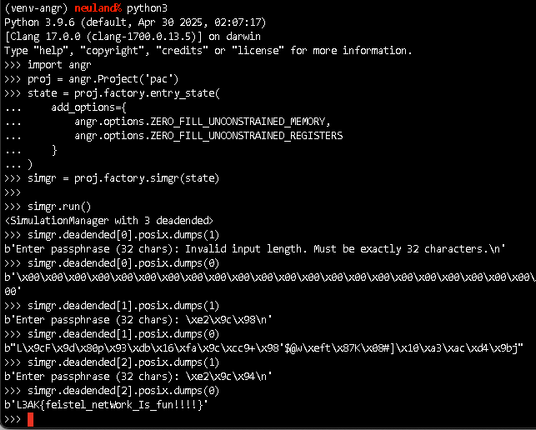
Next module in pwn.college conquered: Return Oriented Programming (ROP). Lessons learned include leaking canary, program and libc ASLR/PIE addresses, (ab)using libc, stack pivoting, abusing long-running "forking" servers and where pwntools and angrop can help in ROP-chain generation.
#ctf #cybersecurity #rop #pwntools #angrop #angr #aslr #pie #canary #leak #pwncollege