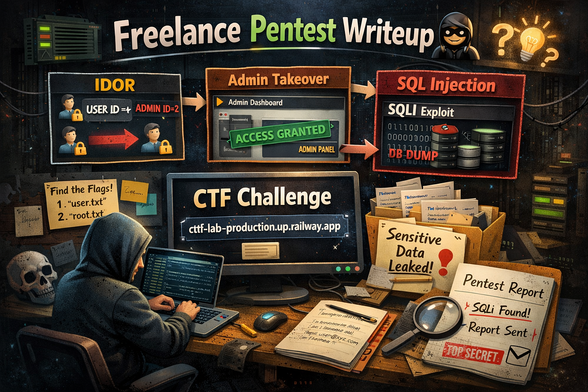
Chaining IDOR to Admin Panel Takeover to SQLI
This article details a series of vulnerabilities: IDOR (Insecure Direct Object Reference), unauthorized access to admin panel, and SQL Injection. The root cause lay in a lack of access control checks on user-supplied input, allowing an attacker to manipulate another user's referral data via IDOR. By chaining multiple IDORs, the researcher gained access to the admin panel. Within the admin panel, an SQL Injection vulnerability enabled the attacker to execute arbitrary SQL queries, leading to unauthorized data access and potential data breaches. The attack vector involved crafting specific referral IDs to exploit the IDOR and manipulate account data, eventually gaining access to the admin panel and executing SQL Injection payloads. The impact was significant, as it allowed full control over the application's data and configuration. The researcher received a $5000 bounty. To fix this, implement proper access control checks on user-supplied input, sanitize and validate all input data, and use parameterized queries to prevent SQL Injection attacks. Key lesson: Always validate and sanitize user input and implement least privilege access controls. #BugBounty #IDOR #SQLInjection #WebSecurity #AdminPanelTakeover