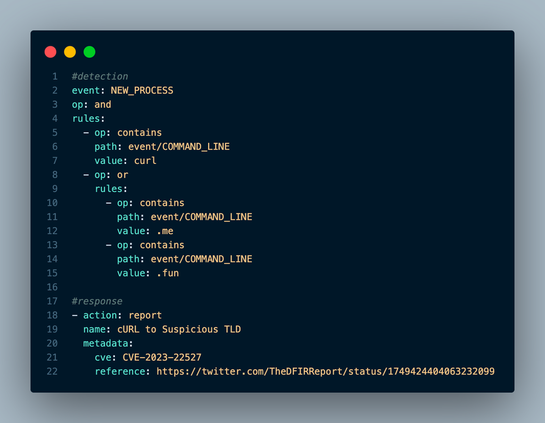
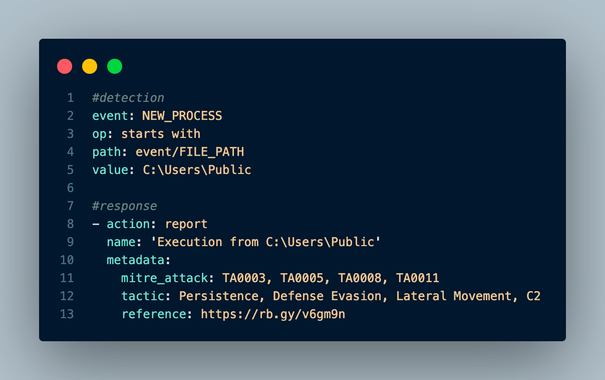
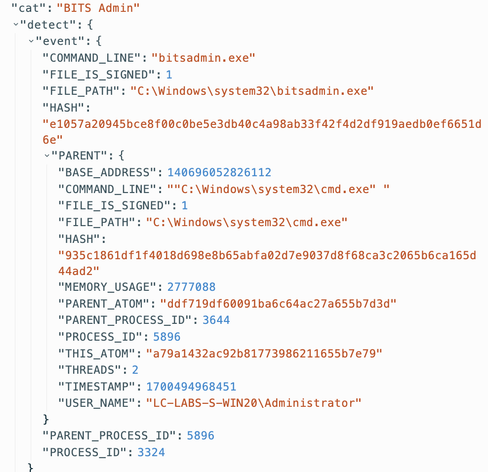
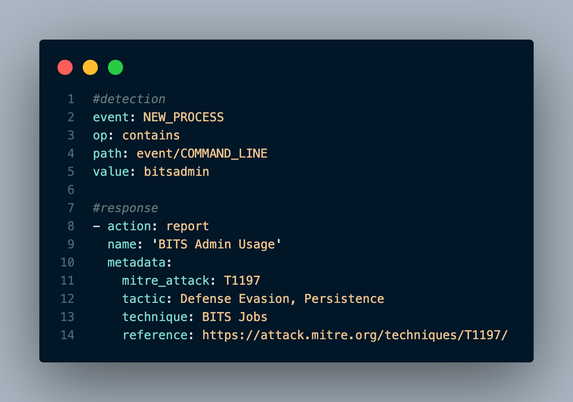
It's Day 11 of #100DaysofLC. Today, we're talking about reported CVE-2023-22527 post-exploitation activity. With D&R rules, let's hunt the post-exploit cURL activity, as the folks at @TheDFIRReport reported.
This LimaCharlie detection rule looks for suspicious cURL calls to .me & .fun domains. This is likely already a great network artifact but can be found via EDR via process execution and command-line parameters. #limacharlie #dfir #DetectionEngineering #ThreatHunting