After more than 9 years, this is my last week at Computest. I've had a great time here, especially in Sector 7, the security research team we started 5 years ago. Highlights for me are winning Pwn2Own with our 0-click Zoom RCE, our last-minute trips to Miami and Tokyo for other Pwn2Own events, and speaking at Black Hat USA, DEF CON, WHY2025 & MCH2022 and so many other places. I am very grateful for getting the chance to do this work, but now it is time for me to do something else and find some new challenges! 🔥
First talk is done! I think it went quite well.
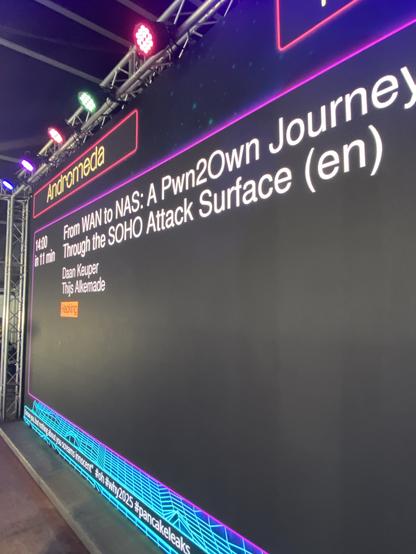
Next one is tomorrow at 19:00 (probably, it has been moved around a lot already) in Andromeda.
#why2025
Made it to #WHY2025!
Last time we had to give 3 presentations, which was a bit much. So this time we’re doing 3 presentations again of course…
About 5 years ago, I reported a vulnerability in iOS allowing apps to spoof the app name when requesting to add a VPN profile. The app could just specify whatever text to show there.
Yesterday, two writeups were posted about other TCC prompts trusting the apps triggering them too much:
https://wts.dev/posts/tcc-who/
https://rambo.codes/posts/2025-05-12-a-privacy-mechanism-that-backfired
It does surprise me that Apple invests so much effort into their sandbox and permission system with the assumption that apps might be malicious, but then keeps messing up the UI around these features.

Can You Really Trust That Permission Pop-Up On macOS? (CVE-2025-31250) | Watch This Space
A security research blog.