> because of the #Linux kernel’s defense in depth measures Mythos was unable to successfully exploit any of these.
https://red.anthropic.com/2026/mythos-preview/
🥂
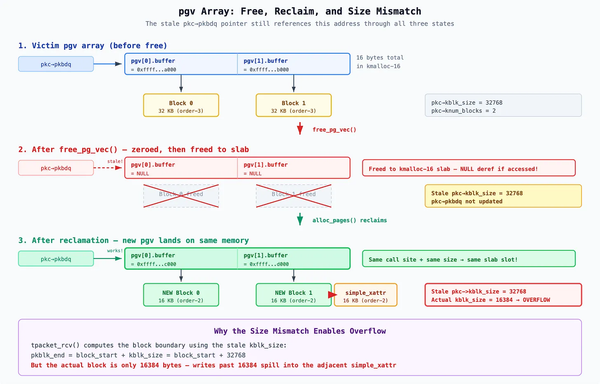
> Where Mythos Preview did succeed was in writing several local privilege escalation exploits.
:(
> We have nearly a dozen examples of Mythos Preview successfully chaining together two, three, and sometimes four vulnerabilities in order to construct a functional exploit on the Linux kernel.
:(
Keep an eye on this query
https://lore.kernel.org/all/?q=Reported-by%3A+Nicholas+Carlini+%3Cnpc%40anthropic.com%3E