| LinkedIn profile | https://www.linkedin.com/in/paulbrodeur |
Paul Brodeur
- 86 Followers
- 121 Following
- 10 Posts
@GossiTheDog oh, yes. As long as the data comes from only one log source, you can use rules engine. API to pull matches is straightforward, and it integrates into the major SOARs. For other more complex use cases BigQuery is required and comes with its own set of limitations.
Listen, it’s not Splunk. But it also doesn’t cost Splunk prices.
Not sure if that answered your question.
My #slides from my #hushcon #talk yesterday. Thanks everybody for coming out! It was great to see / meet y'all!
https://docs.google.com/presentation/d/1CeWI7IIIVJEmrtPkFPnUIUHns2S7gZnchmlTo3ozhEA/edit?usp=sharing
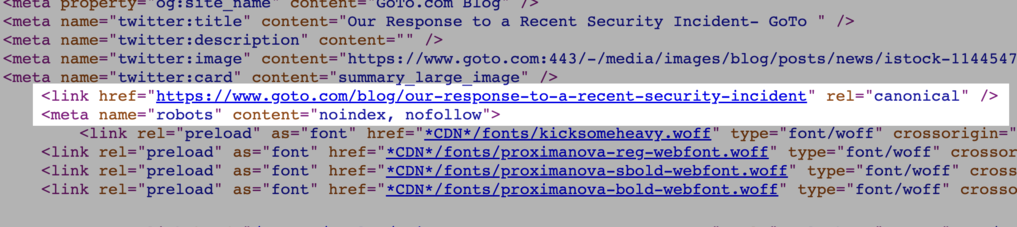
This week, LastPass, and its parent company GoTo, both published blog posts about their recent data breach: http://tcrn.ch/3ucMvBx
But if you search for GoTo's blog post in Google, you won't find it, because GoTo hid its breach notice from search engines using "noindex" code.
How can we waste attackers’ time, attention, and money? Can we inflict psychological damage on them? In essence, can we f*** with them for better resilience outcomes?
Yes we can! Our new paper — led by @dykstra with other fine folks — answers these questions, introducing the concept of “sludge” against attackers for systems resilience: https://arxiv.org/pdf/2211.16626.pdf
Here’s my swing at an #introduction
I’m a Canadian living in Seattle 🇺🇸 which means I pay all the taxes but can’t vote. Might see me post about immigration or Seattle happenings.
I work as the people leader for #SOC and #DFIR and #ThreatIntel at St*rbucks. I run a fully remote team, and I’m passionate about #RemoteWork. You might see me post about vulns or public incidents or whatever else I’m worried about this week. Won’t see me post about my employer.
I’m married, and we love to travel. That content usually ends up on instagram.
I’m going to try to be more active here than I was on the bird site. #BlueTeam #infosec #sectwits