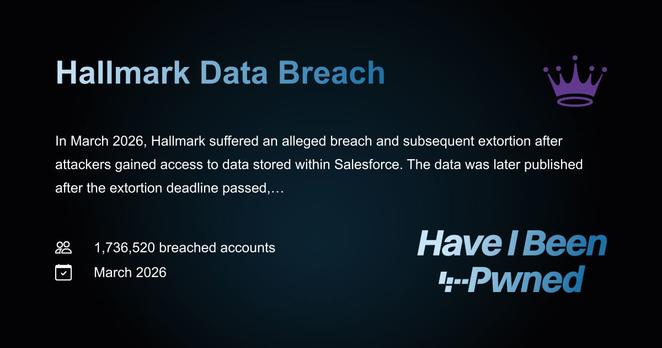
New breach: Hallmark was allegedly breached in March with attackers accessing Salesforce and publishing data this week. It exposed 1.7M unique email addresses with name, phone, physical address & support tickets. 82% were already in
@haveibeenpwned. More:
https://haveibeenpwned.com/Breach/Hallmark
Have I Been Pwned: Hallmark Data Breach
In March 2026, Hallmark suffered an alleged breach and subsequent extortion after attackers gained access to data stored within Salesforce. The data was later published after the extortion deadline passed, exposing 1.7M unique email addresses across both Hallmark and the Hallmark+ streaming service, along with names, phone numbers, physical addresses and support tickets.