| Blog | https://syscall.eu/blog/ |
| Github | https://github.com/trou/ |
Raphaël Rigo
- 307 Followers
- 149 Following
- 462 Posts
Les inscriptions pour le SSTIC 2026 sont ouvertes: https://www.sstic.org/2026/billetterie
Le programme du SSTIC 2026 a été publié: https://www.sstic.org/2026/programme/
Les inscriptions pour le SSTIC 2026 ouvriront le jeudi 26 mars à 14h. Vous trouverez des informations concernant l'ouverture de la billetterie et le déroulement du processus sur l'article de blog dédié. Nouveauté de l'année : l'inscription se fait en donnant les adresses mail des comptes sstic des participants, et plus leur pseudo.
https://blog.sstic.org/2026/03/22/sstic-2026---informations-importantes-sur-les-inscriptions/
RE: https://infosec.exchange/@raptor/116058688911622031
Awesome work by @gaasedelen. Extremely well explained and illustrated.
For once, I'll encourage you to watch the whole video :)
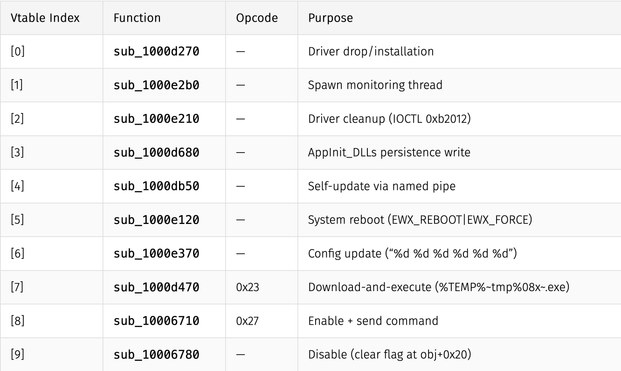
New blog post: Building a Pipeline for Agentic Malware Analysis
Agentic RE + malware analysis with custom skills, MCP tooling, and persistent case state to automate intial triage
Link: https://synthesis.to/2026/03/18/agentic_malware_analysis.html
Github: https://github.com/mrphrazer/agentic-malware-analysis
RE: https://infosec.exchange/@madsquirrel/116238920833196800
Really cool stuff.
http://blog.quarkslab.com/nerd-life-weeks-firmware-teardown-we-were-right.html
A Nerd's Life: Weeks of Firmware Teardown to Prove We Were Right - Quarkslab's blog
In a blog post published last December, we demonstrated how we managed to extract the firmware from a smartwatch by exploiting an out-of-bounds read vulnerability and spying on its screen interface. Follow us on our long and unexpected journey to figure out how this smartwatch can measure heart rate or blood pressure with no visible sensor, the problems we encountered while analyzing its firmware, and how we solved them to uncover The Truth about this device.
https://www.openwall.com/lists/oss-security/2026/03/12/7
Qualys is at it again!