A single bug in an ERC-4337 smart account can be as catastrophic as leaking a private key.
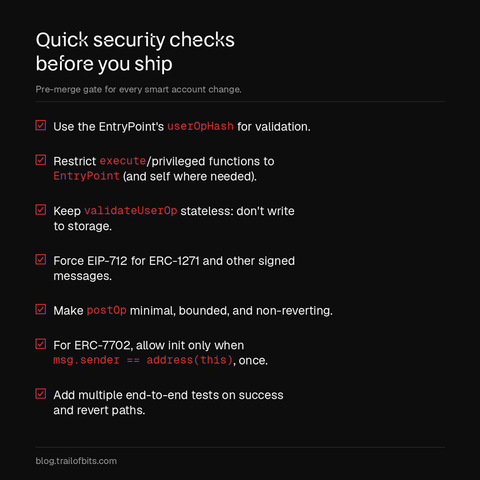
We've audited dozens of smart accounts and found six vulnerability patterns that consistently reappear across codebases.
If you're working with smart accounts, each pattern includes safe code examples so you can reference them for your own implementation: https://blog.trailofbits.com/2026/03/11/six-mistakes-in-erc-4337-smart-accounts/