| Github | https://github.com/tyranid |
| Blog | https://www.tiraniddo.dev/ |
James Forshaw 
- 4.3K Followers
- 162 Following
- 433 Posts
@qdkp @wdormann not sure I agree with the blog posts conclusion that there's no bug. The complex exploit is just using various tricks to make it as reliable as it can but it comes down to defender copying an arbitrary file through a symlink as SYSTEM.
As for the redirection mitigation, god knows why they don't turn it out. It wouldn't shock me if it's some concern that it'll break some enterprise consumer using junctions , or maybe malware could hide itself.
@wdormann actually going back it looks to me like Defender makes a copy of the file into a location the user can read, so not passing back a handle.
Also not saying MSRC are in the right in any way, but certainly a super complex PoC combined with not 100% reliability won't have helped. Ideally a simple description should be enough for them but that's now how MSRC operate now. Maybe they can get Project Glasswing to the work for them in the future :)
@wdormann oh I see, it passes back a handle. I assumed Defender did something to the file, then the unprivileged process opened the file. And yeah if it passes back a read-only handle then the code can parse out the SAM's contents as everything else needed to decrypt the hashes is accessible without any privileges (bizarre IMO).
No doubt it'd be relatively easy to narrow this down to something simpler as a PoC, perhaps that didn't help their case with MSRC who as you point out have become somewhat lazy in their triage process.
🆕 New blog post!
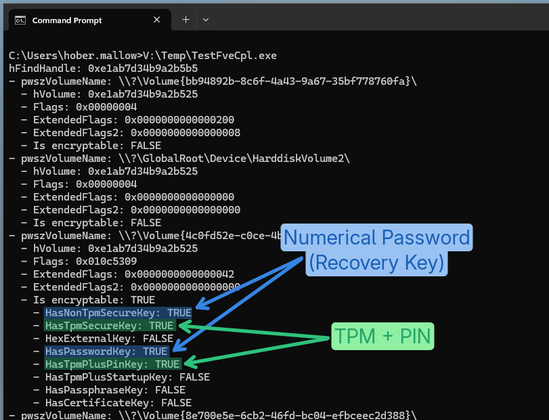
"BitLocker's Little Secrets: The Undocumented FVE API"
A small Windows RE adventure to figure out how to get the status and configuration of a BitLocker protected drive programmatically and without admin privileges.
Now also implemented in PrivescCheck! 🔥
👉 https://itm4n.github.io/bitlocker-little-secrets-the-undocumented-fve-api/
Interested in attending BlueHat 2026? Registration is closing TODAY and is extremely limited, so please fill out the application to attend here if interested!
https://microsoft.eventsair.com/bluehat2026/reg/Site/Register