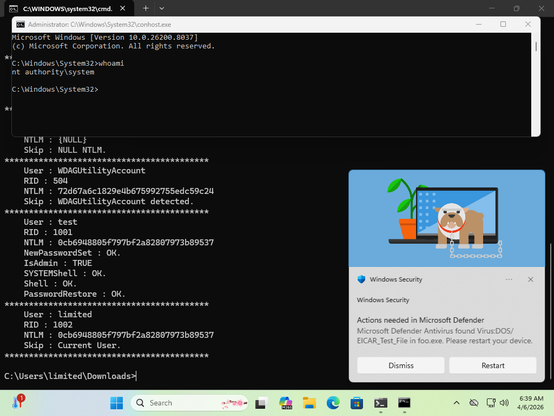
There's a new Windows 0day LPE that has been disclosed called BlueHammer. The reporter suggests that it's being disclosed due to how MSRC operates these days.
MSRC used to be quite excellent to work with.
But to save money Microsoft fired the skilled people, leaving flowchart followers.
I wouldn't be surprised if Microsoft closed the case after the reporter refused to submit a video of the exploit, since that's apparently an MSRC requirement now. 😂
Anyway, yeah, it works. Maybe not 100% reliably, but well enough...