thepwnicorn
- 68 Followers
- 71 Following
- 719 Posts
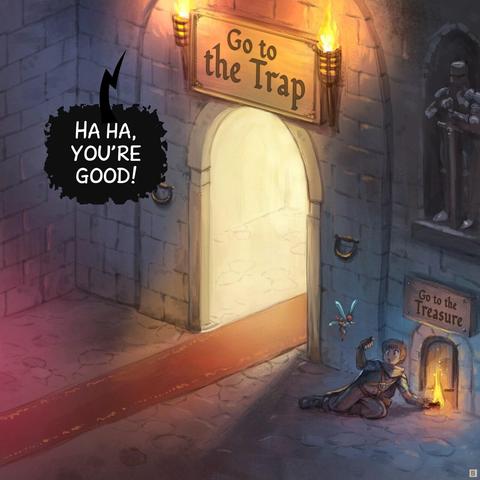
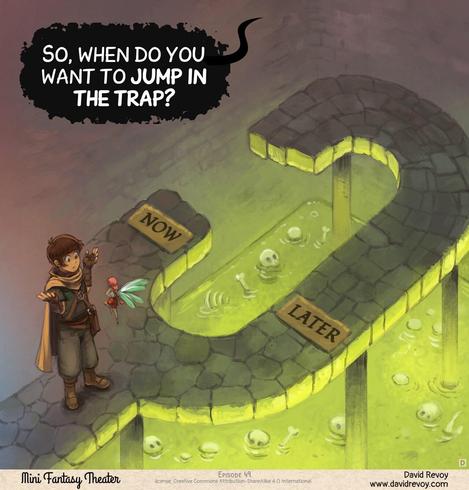
The Dungeon of Dark Patterns
Sources and bonus timelapse: https://www.peppercarrot.com/en/miniFantasyTheater/049.html
I just posted a blog, it is 100% nicer and more restrained than our development team would have posted. Read between the lines, people.... ;-)
https://www.isc.org/blogs/2026-04-16-How-to-report-a-vulnerability/
Well this is truly bad. US national level OS-level age verification bill. https://www.congress.gov/bill/119th-congress/house-bill/8250/all-info
The text of it isn't out yet.
EDIT: Well the text is now out and it's as bad as you could imagine. It's not even just that you need to verify your age to access a website... operating systems must verify your age to let you *use a computer at all*
EDIT EDIT: Thanks to @Andres4NY for pointing out that it also holds responsible anyone who has any software shipped on the operating system of a computer, meaning FOSS developers eveywhere
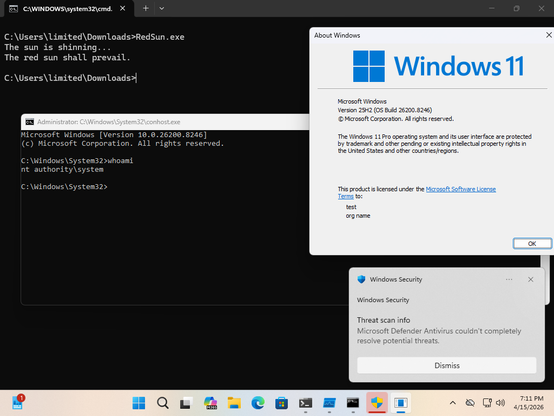
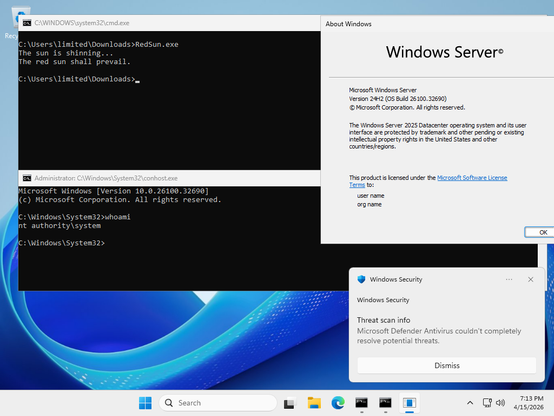
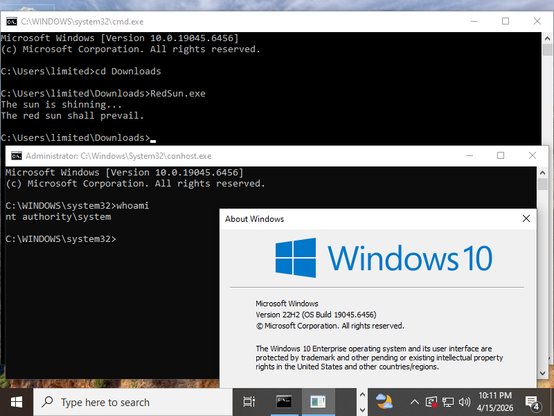
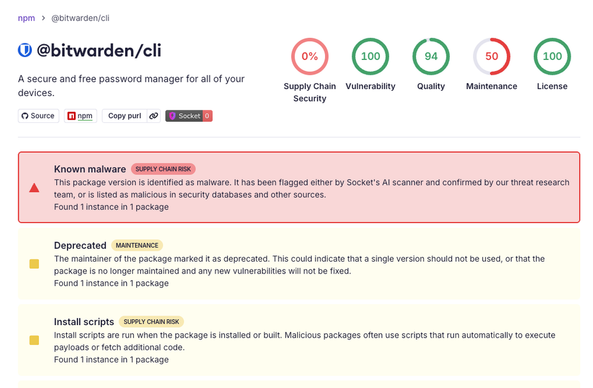
From the same author as BlueHammer we now have RedSun.
This works ~100% reliably to go from unprivileged user to SYSTEM against Windows 11 and Windows Server 2019+ with April 2026 updates, as well as Windows 10, as long as you have Windows Defender enabled. Any system that has cldapi.dll should be affected.
HAHAHAHA
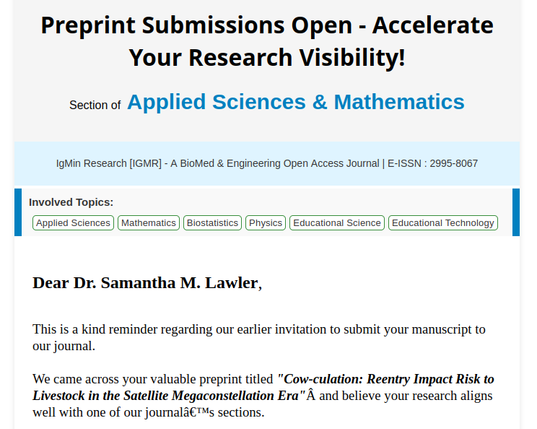
Predatory journals do not know how to handle April Fool's Day papers (like this one https://arxiv.org/pdf/2603.29324) on the arxiv...
When you read about Bans of Social Media for Teens and Age Verification, you must remember what it truly means:
• Official identification of every adult using social media.
• Deanonymization of every account, endangering groups that often rely on pseudonymity for safety, such as victims of domestic violence, victims of stalkers, people of color, and LGBTQ+ people.
• Putting every adult at great danger of exploitation, fraud, and identity theft by forcing them to share their official ID with a for-profit third-party company with no incentive to protect it. Breaches have already happened.
• Constructing a system of mass surveillance to attach every comment on social media to a legal identity. Effectively allowing authoritarian governments to silence their critics and opposition.
• Potential for dystopian censorship and cutting off means of organization for groups of resistance to oppressive regime and organizations.
• Endangering children online by putting a clear identification beacon over every child or family with children online.
• Endangering the data of children who will inevitably try to pass as adults, and have their information collected by the third-party for-profit company.
• Diminishing the value of official identification due to the inevitable data breaches, eventually pushing the system to require even more intrusive identification techniques, such as iris scans and fingerprints.
• Installing a system of mass surveillance capable of attaching even more information to everyone's legal identity. With a potential to built list of people in certain groups, and scale-up state censorship and discrimination in unprecedented ways.
• The list goes on and on.
This isn't about protecting the children.
It never was.
Do not be duped by this excuse used to convince you to let go of your human rights. They are only trying to manipulate people lacking information.
Stay informed on the issues related to Age Verification, and push back for your rights to privacy and democracy.
The future depends on us.
#AgeVerification #Privacy #HumanRights #MassSurveillance #Authoritarianism


 🛡️
🛡️