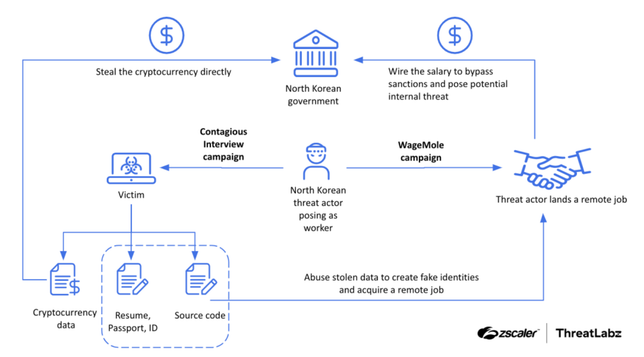
Just dropped our research on DPRK's campaigns: Contagious Interview & WageMole.
Key takeaways:
1️⃣Threat actors are rapidly evolving tools in Contagious Interview.
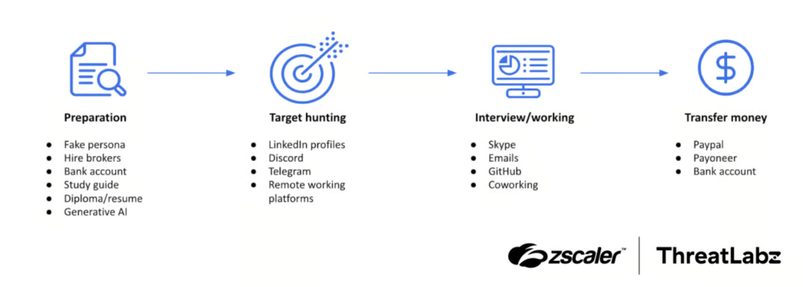
2️⃣Successful infection across platforms in record time.
3️⃣WageMole shows in-depth interview prep & precise target selection.
4️⃣They're enhancing interview prep with data stolen from Contagious Interview & Generative AI tech.