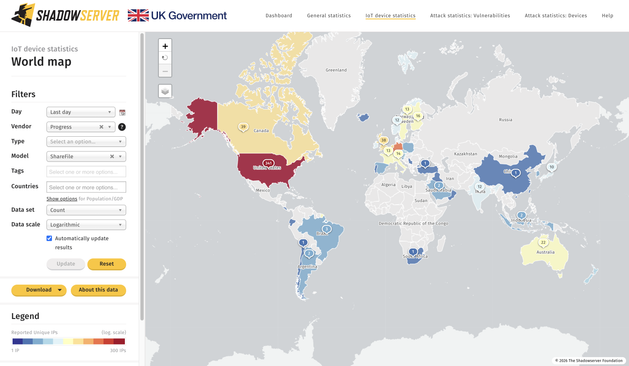
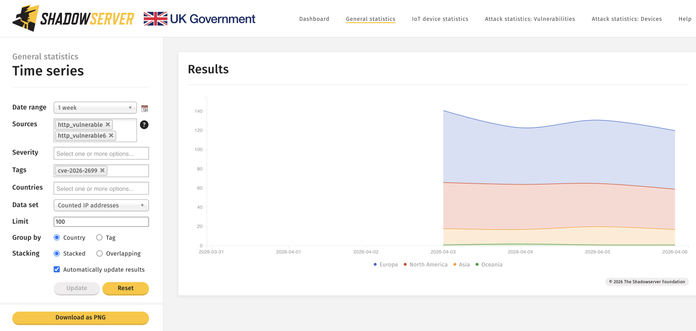
We added Progress ShareFile fingerprinting to our scans & reports with 784 unique IPs seen exposed on 2026-04-02. watchTowr recently disclosed details behind an RCE CVE-2026-2699 & CVE-2026-2701 exploit chain affecting ShareFile. Make sure to apply the latest patch!
Raw IP data in Device ID reports, with device_vendor set to Progress & device_model to ShareFile: https://www.shadowserver.org/what-we-do/network-reporting/device-identification-report/
Thank you to Validin for the collaboration!
Dashboard World Map view: https://dashboard.shadowserver.org/statistics/iot-devices/map/?date_range=1&vendor=progress&model=sharefile&data_set=count&scale=log&auto_update=on
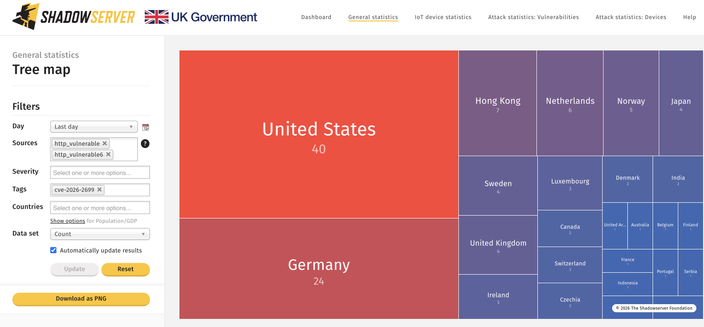
Dashboard Tree Map view:
https://dashboard.shadowserver.org/statistics/iot-devices/tree/?date_range=1&vendor=progress&model=sharefile&data_set=count&scale=log&auto_update=on
Top affected: US, Germany
Note: we are just sharing the exposed population, there is no vulnerability assessment
Patch: https://docs.sharefile.com/en-us/storage-zones-controller/5-0/security-vulnerability-feb26
CVE-2026-2699 NVD entry: https://nvd.nist.gov/vuln/detail/CVE-2026-2699
CVE-2026-2701 NVD entry:
https://nvd.nist.gov/vuln/detail/CVE-2026-2701